OSINT Writeup - 2026 Edition
Table of contents
In this article, we present the different solutions to the Jeanne d’Hack CTF 2026 challenges for the OSINT category.
The writeups are organized by difficulty: Introduction, Easy, Medium, Hard, then Extreme.
Introduction
Intro - Jeanne d’Arcade
The challenge sources are available here.
Description
Jeanne d’Arcade is the undisputed leader of the Guardians of Arcane. A pixel fan created a mosaic portrait of her.
- What is the number written on the flag in the mosaic?
- In which city was this mosaic installed?
- What is the name of the artist?
Flag format:
JDHACK{666_paris_bansky}
Solution
We are given a picture of a street-art piece like this:

By performing a reverse image search on Google or another image-search engine, we can quickly obtain the different pieces of information we need:

For example, we can find everything on this page: https://france3-regions.franceinfo.fr/centre-val-de-loire/loiret/orleans/street-art-mifa-mosa-signe-sa-100e-mosaique-met-honneur-jeanne-arc-1554550.html
From there we get:
- What is the number written on the flag in the mosaic?: 100
- In which city was this mosaic installed?: Orléans
- What is the name of the artist?: Mifamosa
Flag: JDHACK{100_orleans_mifamosa} or JDHACK{100_orleans_mifa_mosa} (both were accepted).
Difficulty: Easy
YouTube Game
The challenge sources are available here.
Description
I bought some retro games at a flea market. A YouTuber who made a video 15 years ago about one of the games shown in the picture says they were inspired by an existing concept when they started making videos. What is the acronym for that concept?
Flag format:
JDHACK{nasa}
Solution
We have a picture of several retro games:

We need to find a YouTuber who made a video about one of these games around 15 years ago, and who states that they were inspired by an already existing concept for their early videos. The flag is the acronym of that concept.
By searching for the visible games or using reverse image search, we can track down corresponding videos. One video from around 15 years ago on YouTube is, for instance: https://www.youtube.com/watch?v=AwNn5tPgKg8&t=14s
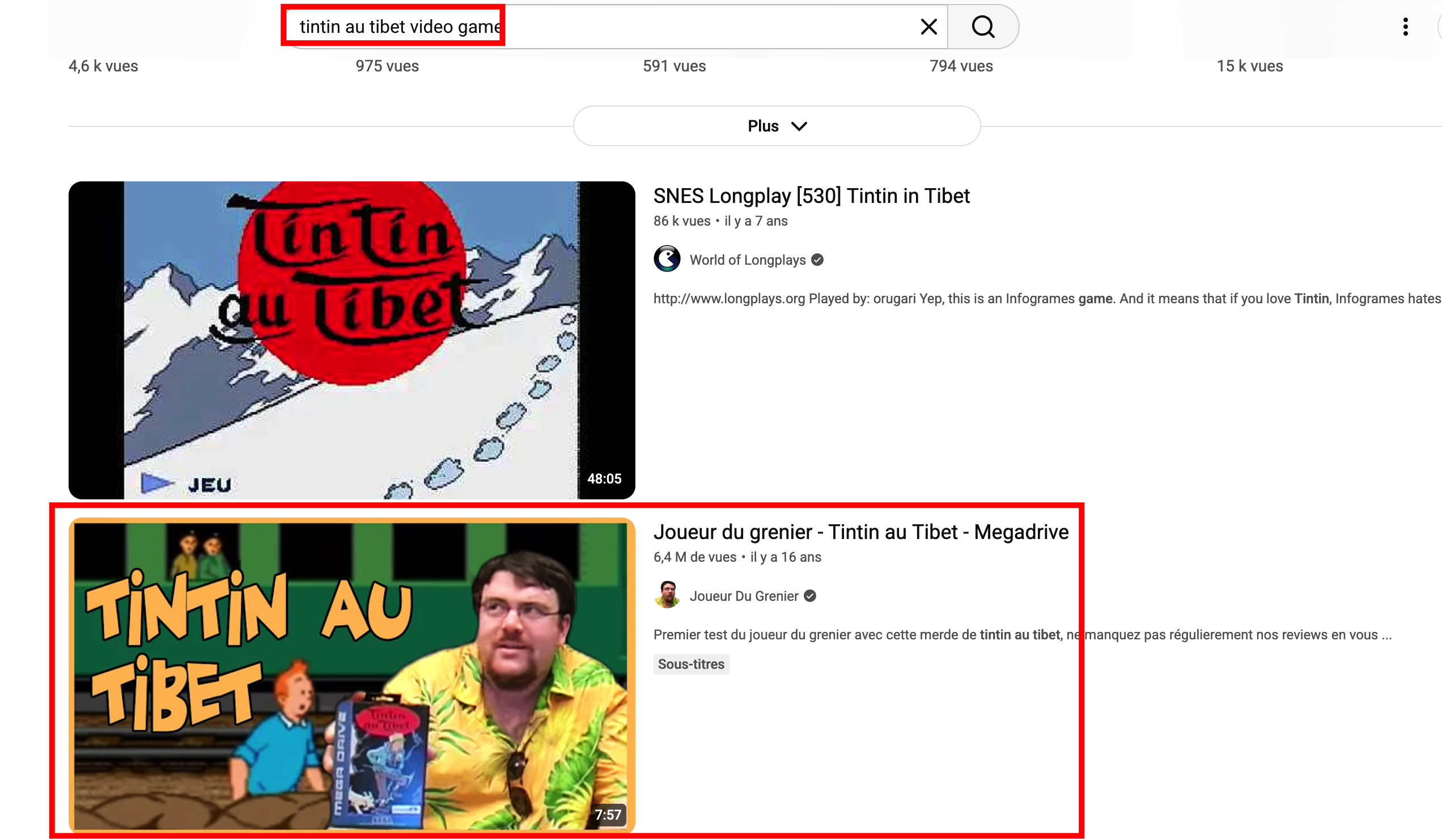
In this game’s video, we can find in the description the information we are looking for:
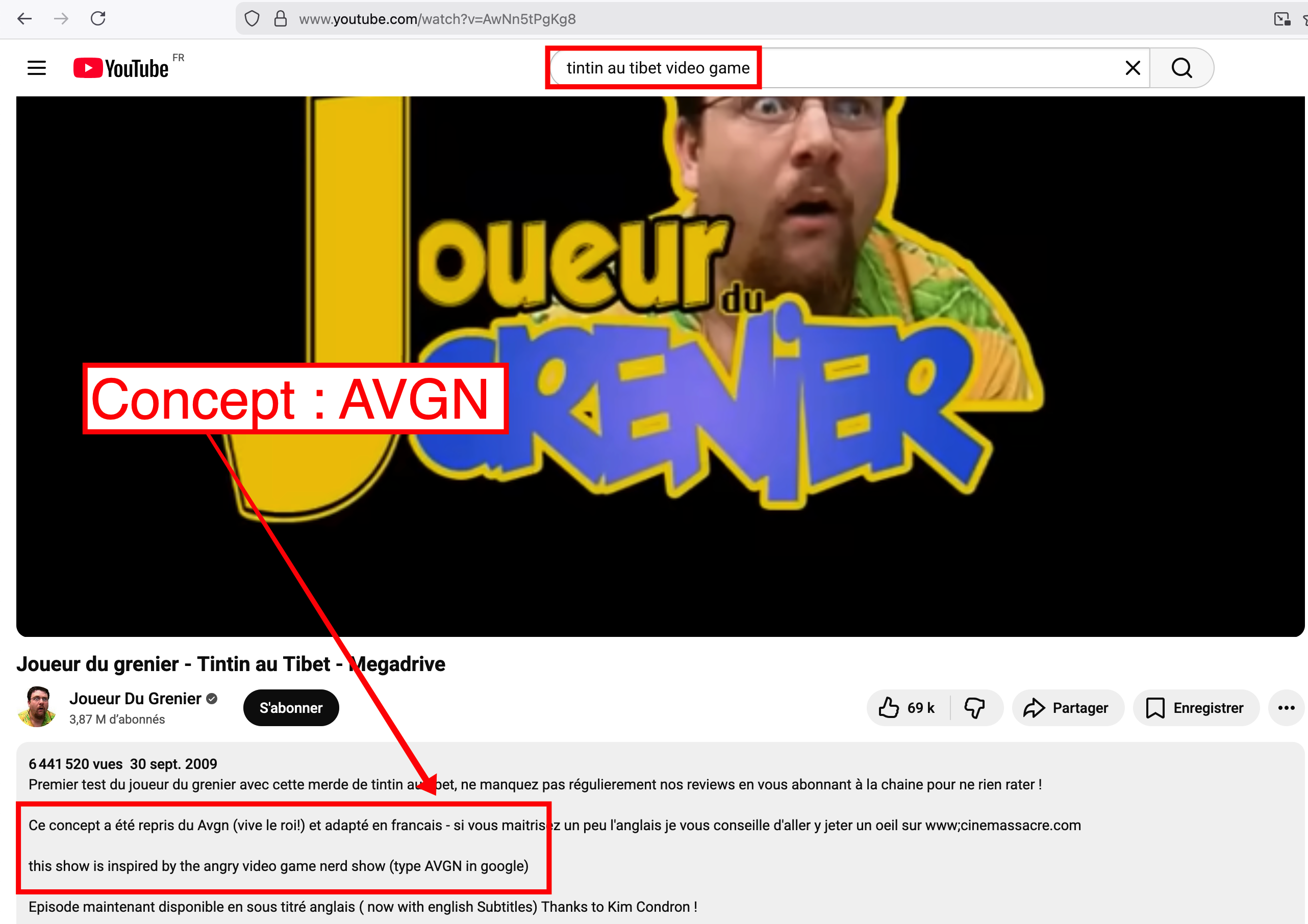
The YouTuber says they were inspired by the AVGN (Angry Video Game Nerd) concept, whose acronym is the expected answer.
Flag: JDHACK{avgn}
Game Over, Press Drink to Continue
The challenge sources are available here.
Description
A retro-gaming bar shut down in November 2024. It was famous for its movie-inspired cocktails and unique atmosphere with retro video games. I once had a “Mister Jack” cocktail there. Which princess had a church built on the site where this bar now stands?
Flag format:
JDHACK{princesse_peach}
Solution
We are given a picture (of the bar or related to it):
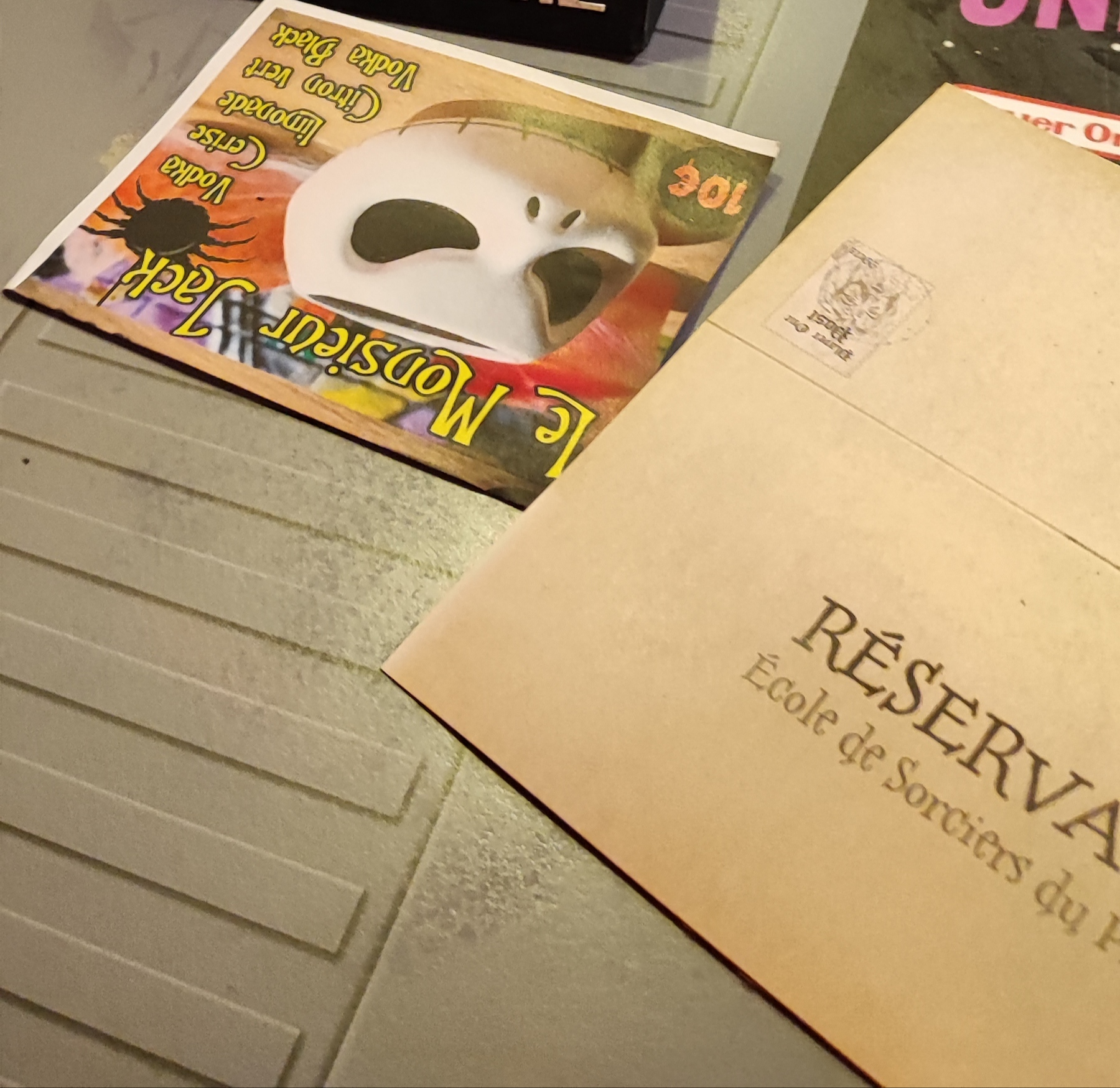
The goal is to find the location of this retro-gaming bar, then determine which princess had a church built on this site.
Step 1 — Locate the bar
A simple Google search (keywords like “Mister Jack cocktail retro gaming bar”) or an image reverse search might not be enough. We then need to inspect the EXIF metadata of the picture: photos taken with a phone or camera often contain GPS coordinates, location names, date, or device information.
- Use a tool such as ExifTool (
exiftool image.jpg), any online EXIF viewer, or your OS file properties. - Look for GPS coordinates, place name, or address in the metadata.
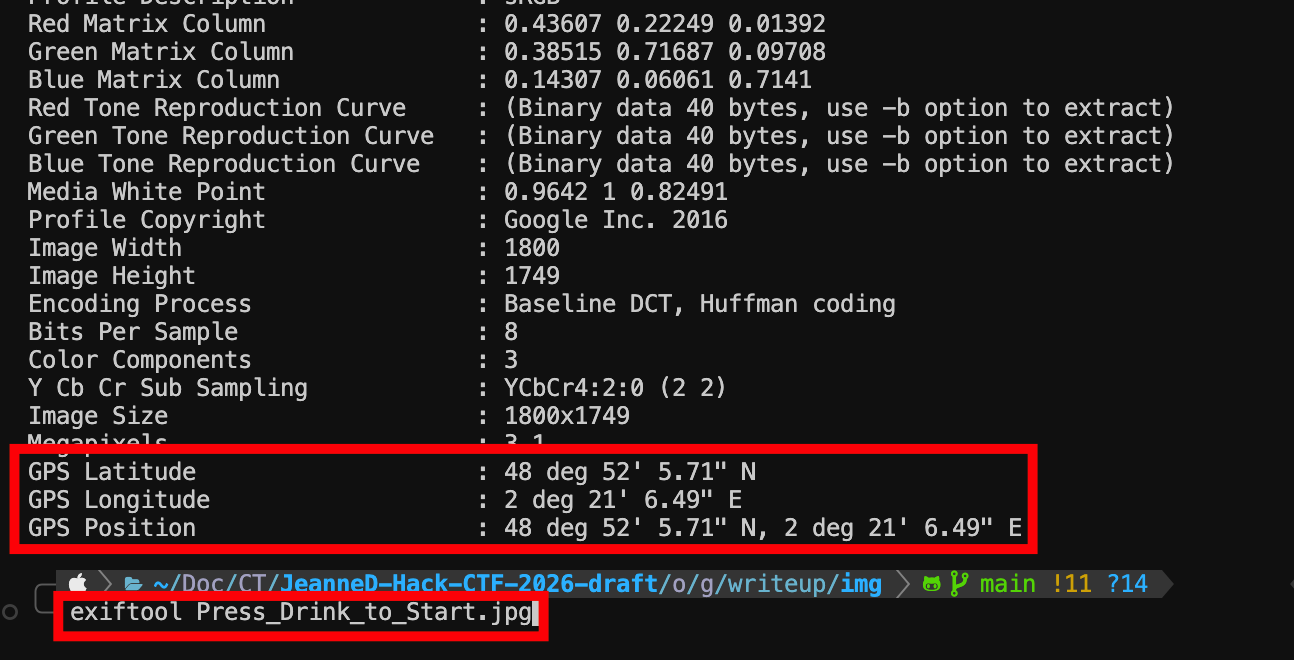
The EXIF metadata gives us the coordinates 48°52'5.71" N, 2°21'6.49" E (or in decimal 48.868253, 2.351803). Entering these into Google Maps brings us to the Player One bar:
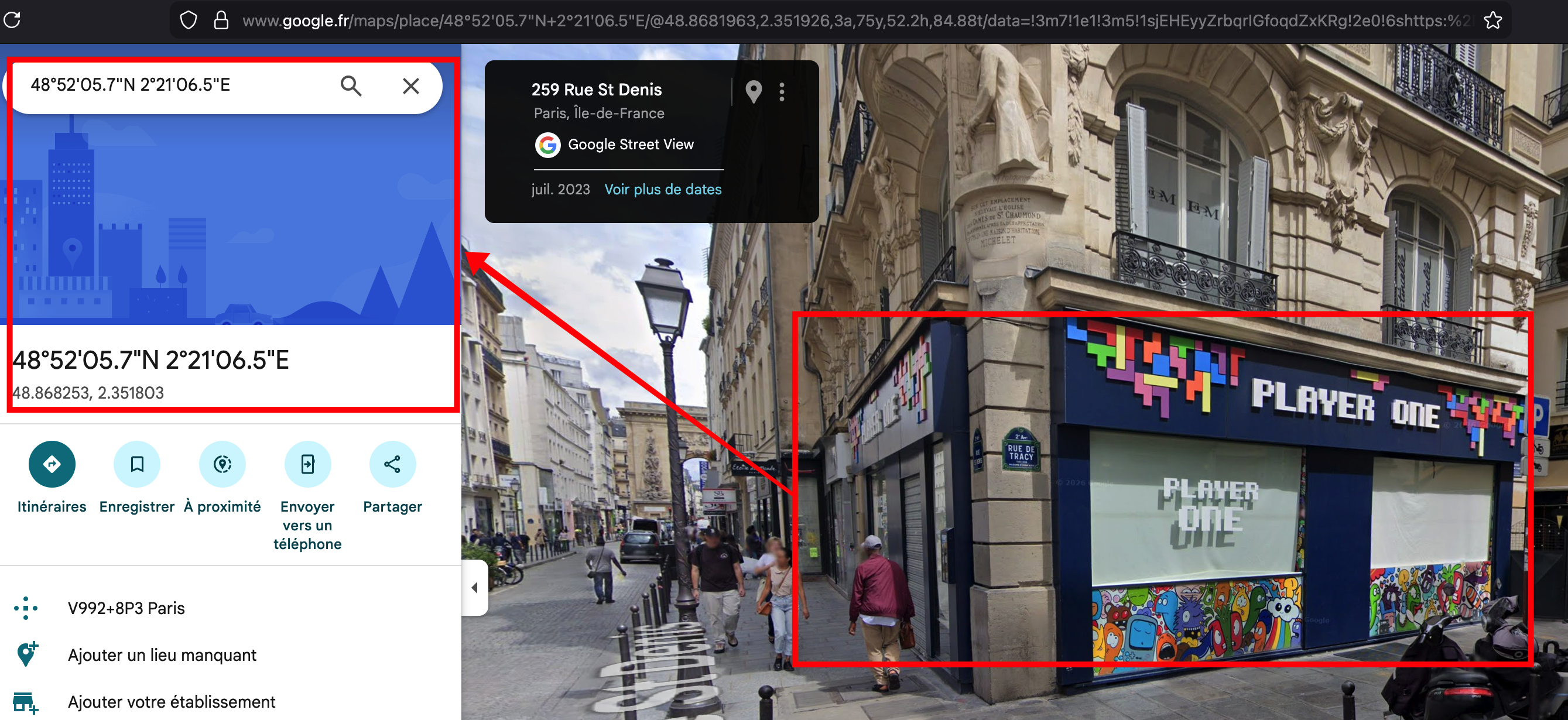
Step 2 — Church and princess
By zooming in on Google Maps or searching around, we get the name of the church located on this site: the Église des Dames de Saint-Chaumont.
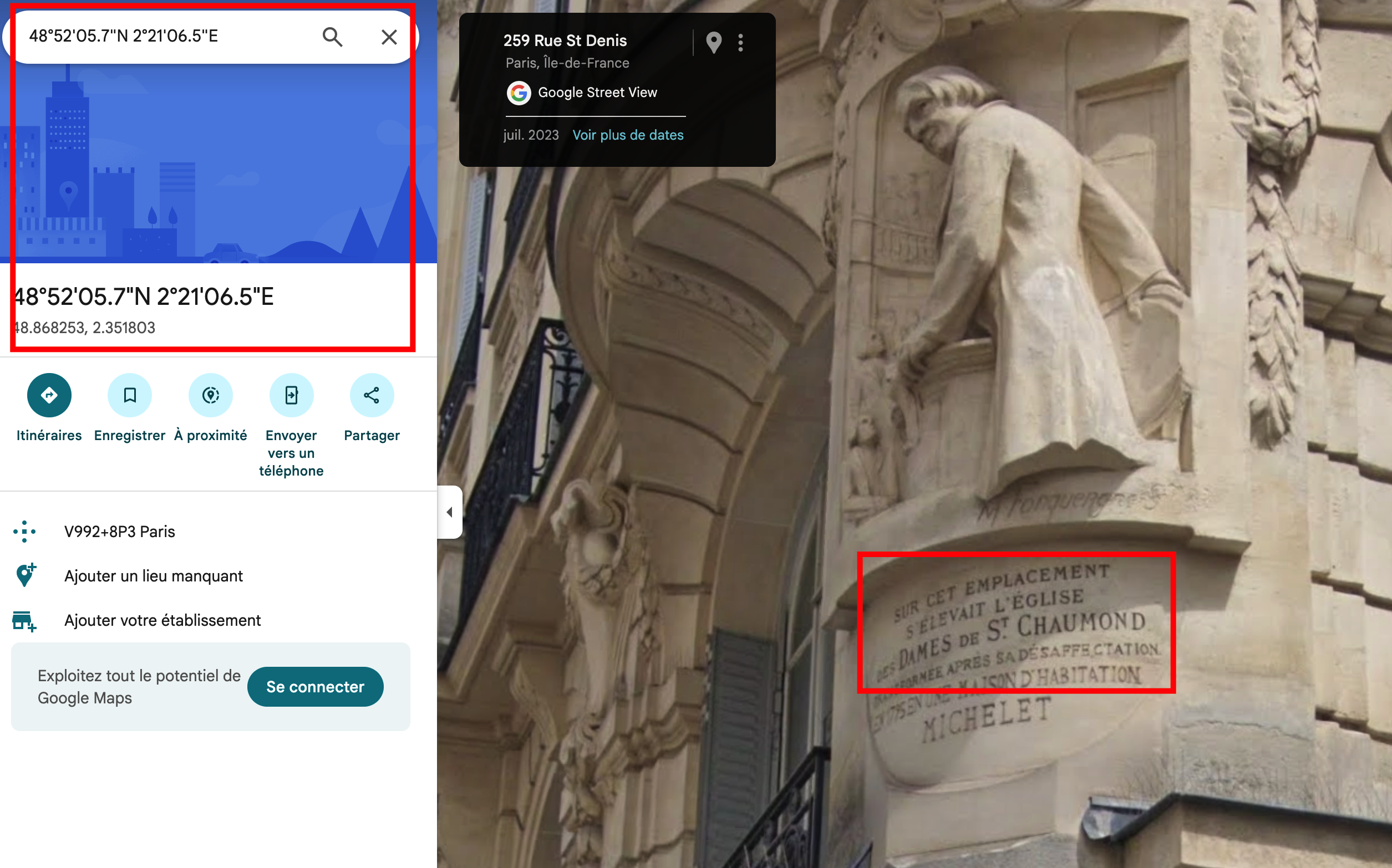
Searching this church leads us to the Couvent des Filles de Saint-Chaumont:
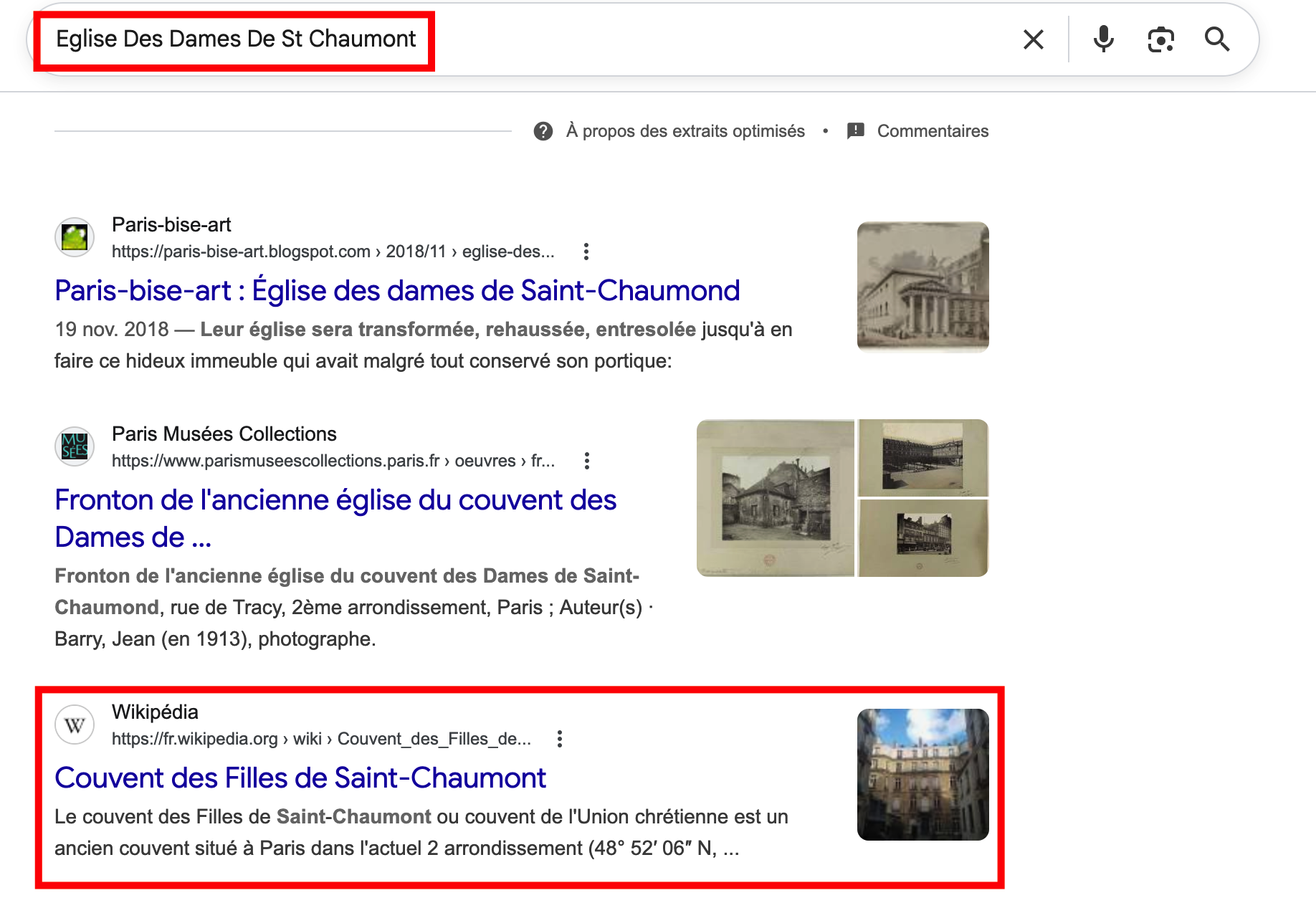
On the corresponding Wikipedia page, we find the name of the princess who had this church built:

It is Marie-Anne de Conti (Princess of Conti). The flag is therefore princesse_de_conti.
Flag: JDHACK{princesse_de_conti}
Map Explorer
The challenge sources are available here.
Description
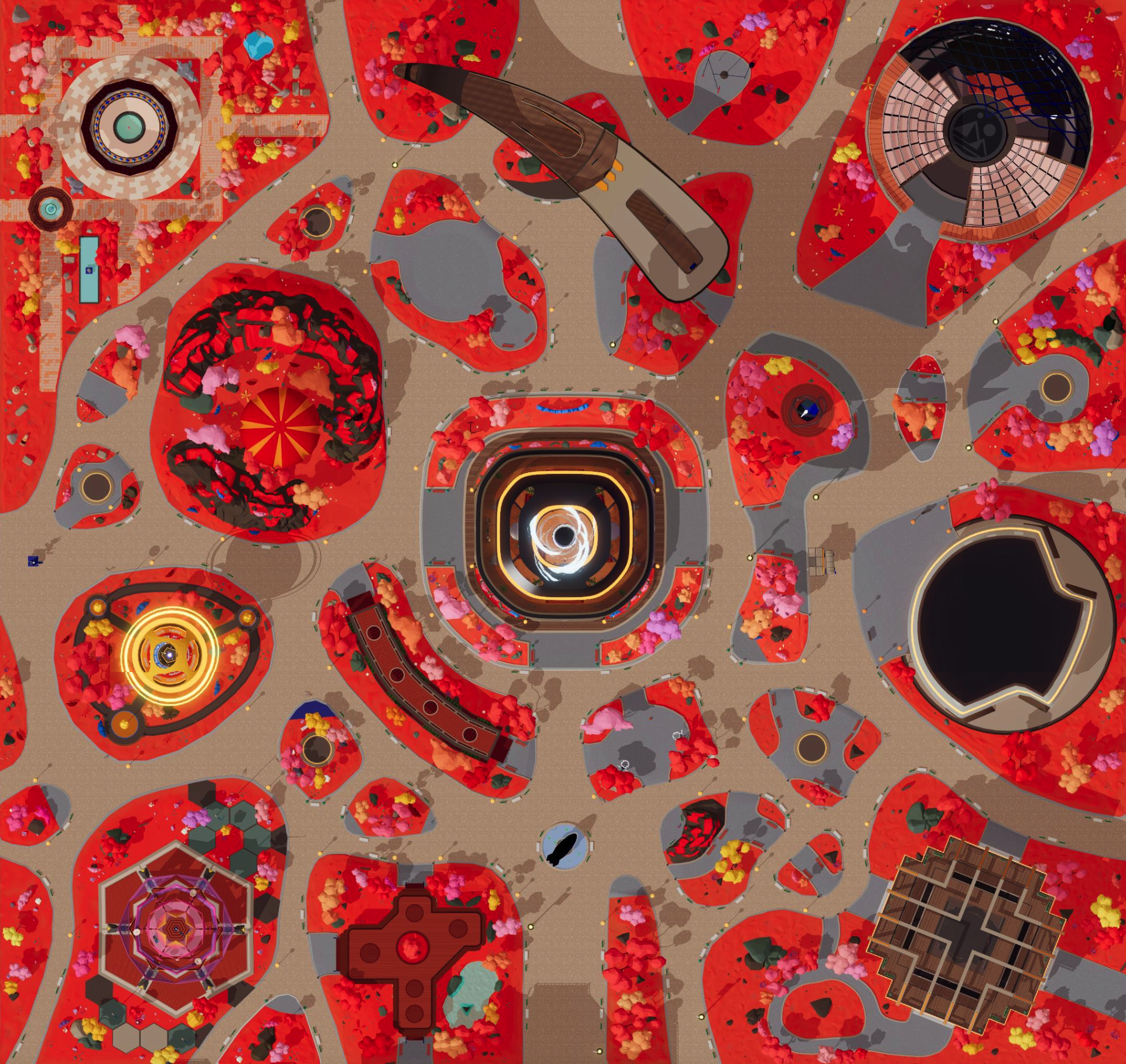
You are browsing your saved game screenshots and find two enigmatic images. Identify the two locations. The flag is made of the desert location name, and the second part is the world in which the other image is located.
Flag format:
JDHACK{desert_location.world}
Solution
We are given two mysterious images from saved-game screenshots.
Image 1 — Desert location:

Image 2 — Other world:
Step 1 — Identify the desert location
The desert landscape can be associated with Cyberpunk 2077, more specifically with a mod that adds this area. A search leads us to: https://www.nexusmods.com/cyberpunk2077/mods/24197?tab=files
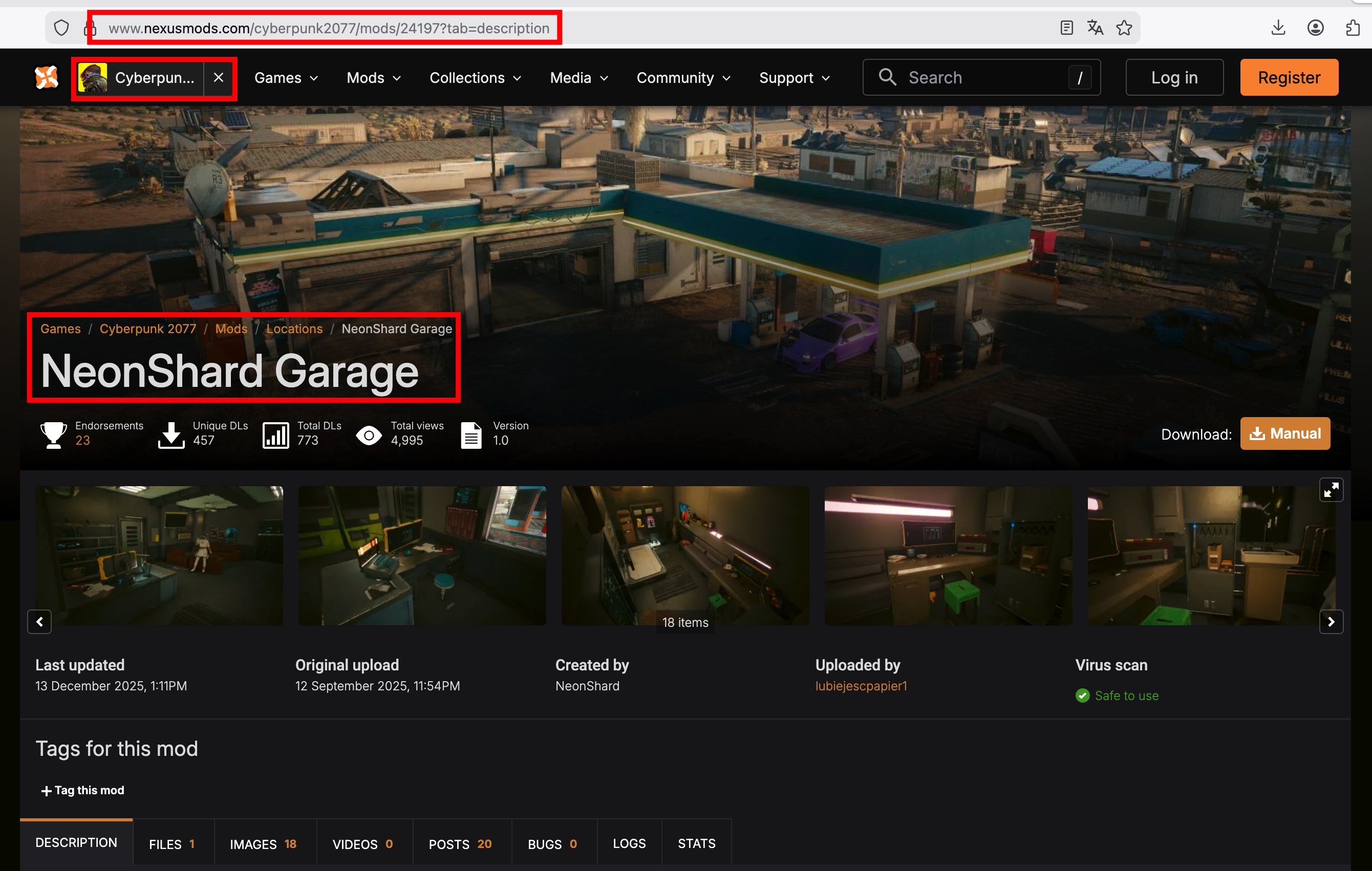
In the comments about this mod, we can see how the desert town is named:
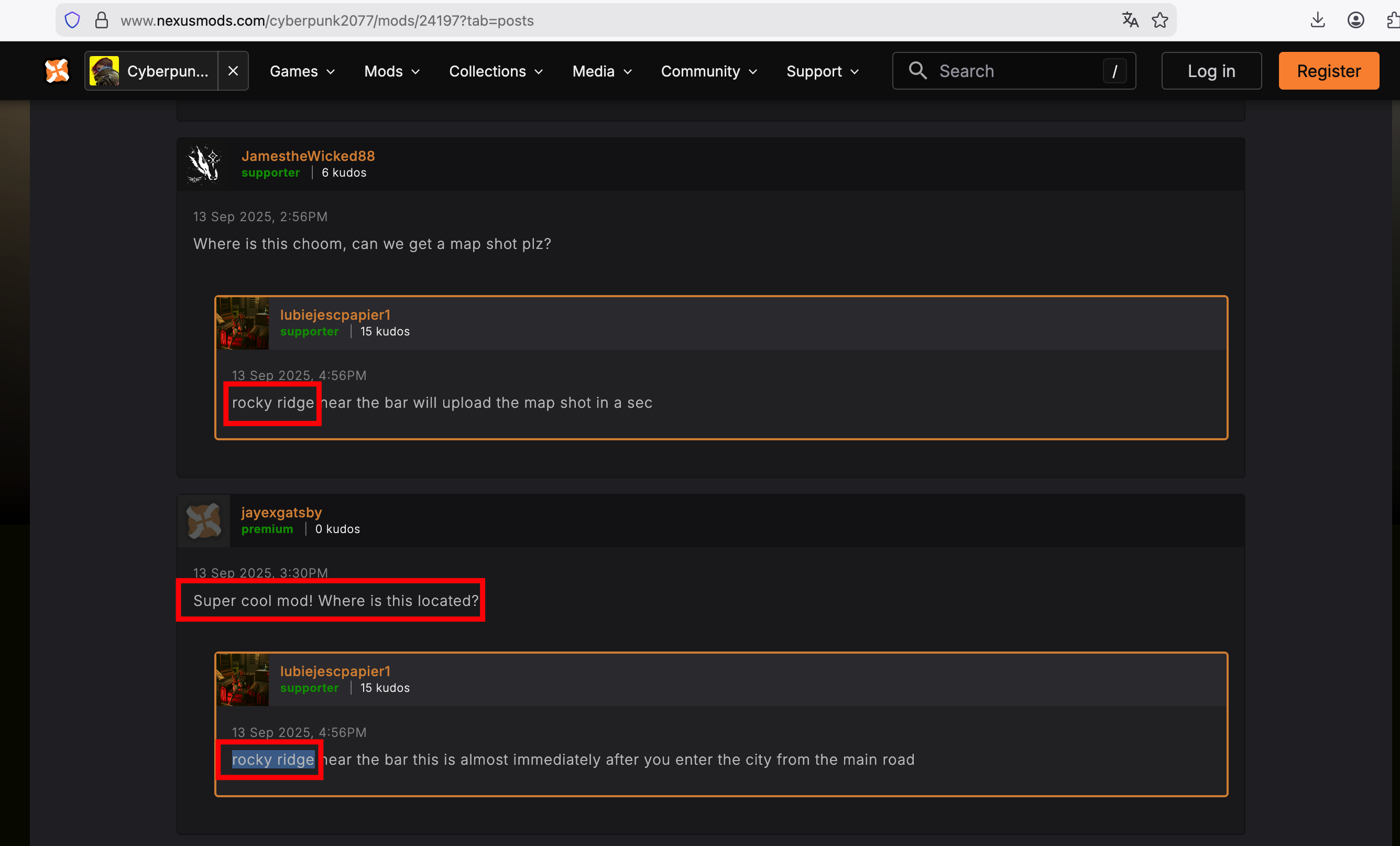
The desert location is Rocky Ridge.
Step 2 — Identify the world of the second image
When searching on the internet for the second image, we find: https://x.com/genesiscitymap
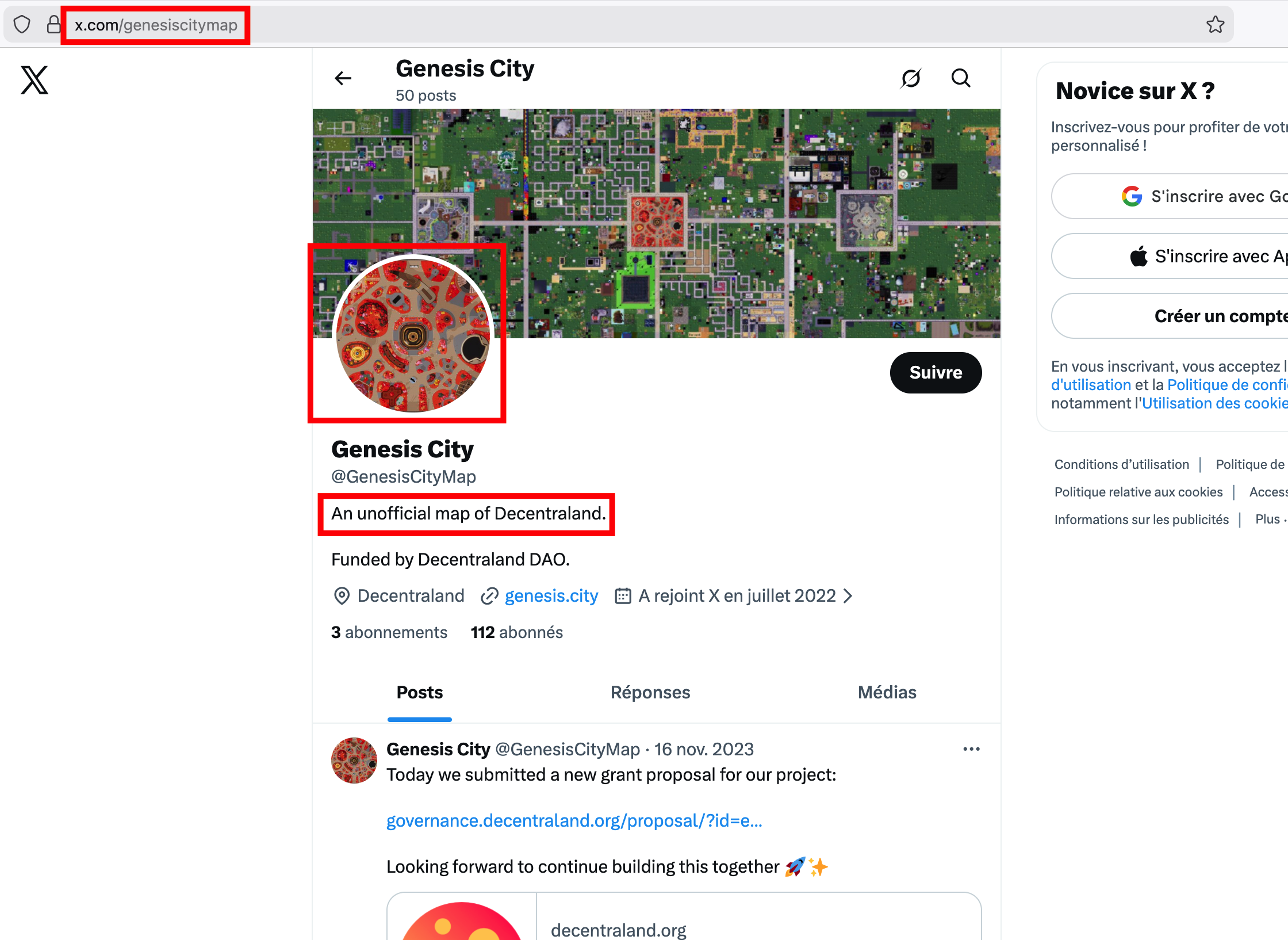
The world shown by this map is called Decentraland.
Flag: JDHACK{rocky_ridge.decentraland}
Difficulty: Medium
Champ de Pixels Mystère (Mysterious Pixel Field)
The challenge sources are available here.
Description
I met someone a few months ago on an old multiplayer game server. We chatted all evening and then I was never able to find them again. Their nickname was LuigiLag42. They told me about a geek/pixel-art artist they admired a lot, but I no longer remember this artist’s name.
- Starting from this nickname and clues you can find online, recover the name of the artist they were talking about.
- The artwork you need to identify pays tribute to another artist. What is the country of origin of this second artist?
Flag format:
JDHACK{mr_pixel_new_zealand}
Solution
We start with the nickname LuigiLag42. We can use OSINT tools such as Sherlock to find where this username is used.
Example with Sherlock:
sherlock LuigiLag42
We find, for example, a Gamespot profile:
[+] Gamespot: https://www.gamespot.com/profile/LuigiLag42/
On this profile, we find a specific image:

This image shows a sunflower with coordinates: 48°51'44.3"N 2°19'13.7"E (near Paris).
Using these coordinates and the pixel-art style, we can search for the street artist. On Google Earth, we can see the following street art:
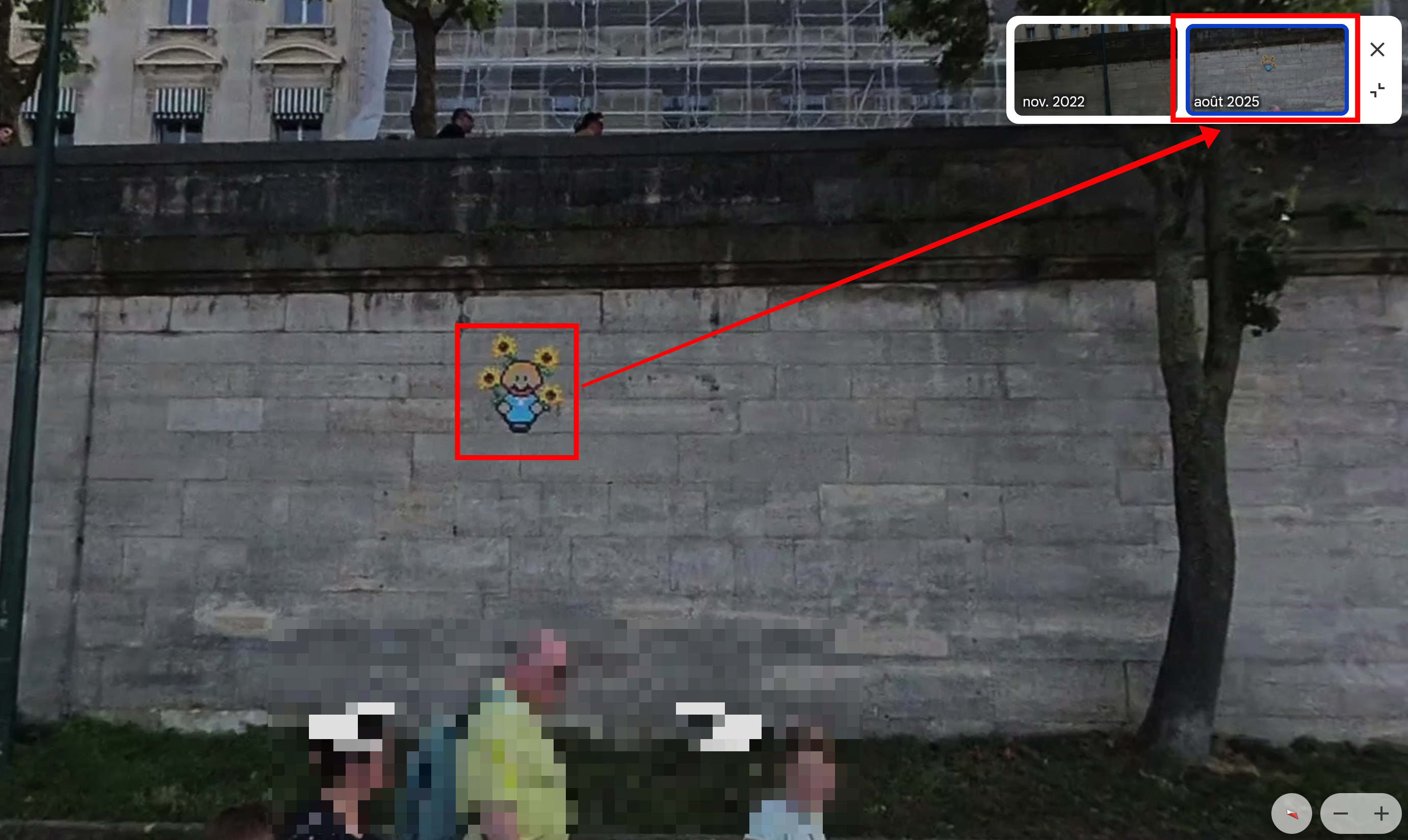
We could also have found it through this map: https://pixel-hunting.com/ou-trouver-des-mosaiques-du-street-artiste-in-the-woup-a-paris-notre-carte-gratuite/
The artist is In The Woup, and the artwork (a Mario / Van Gogh crossover) pays tribute to Vincent van Gogh, who came from the Netherlands.
Flag: JDHACK{in_the_woup_pays_bas}
Difficulty: Hard
Shadows of the End (Minecraft)
The challenge sources are available here.
Description
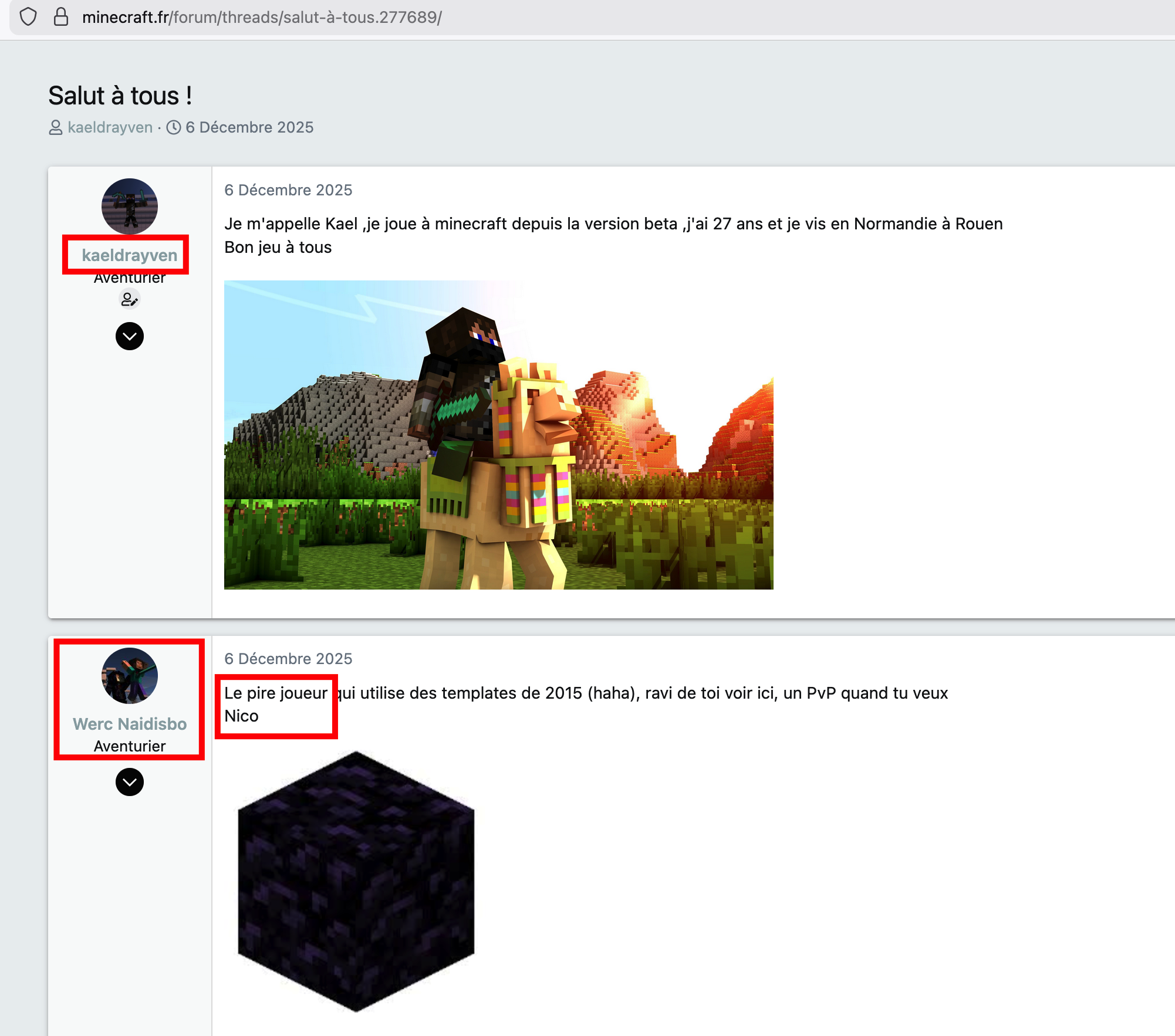
In the world of video games, rumors spread at lightning speed. My friend Kael Drayven finds himself involved, against his will, in a wave of baseless accusations and harassment in connection with his favorite game. Anonymous messages posted on various forums and social networks suggest that an organized group is deliberately trying to damage his reputation. What are the first names of the three members of this group?
Flag format:
JDHACK{n..._g..._e...} (with the full first names)
Solution
We start from the name Kael Drayven. The goal is to find the first names of the three people who form the group that is harassing him.
Step 1 — Find Kael’s accounts and email
A search on social networks reveals Kael Drayven on Bluesky (e.g. endermanhunter.bsky.social) and on Facebook.
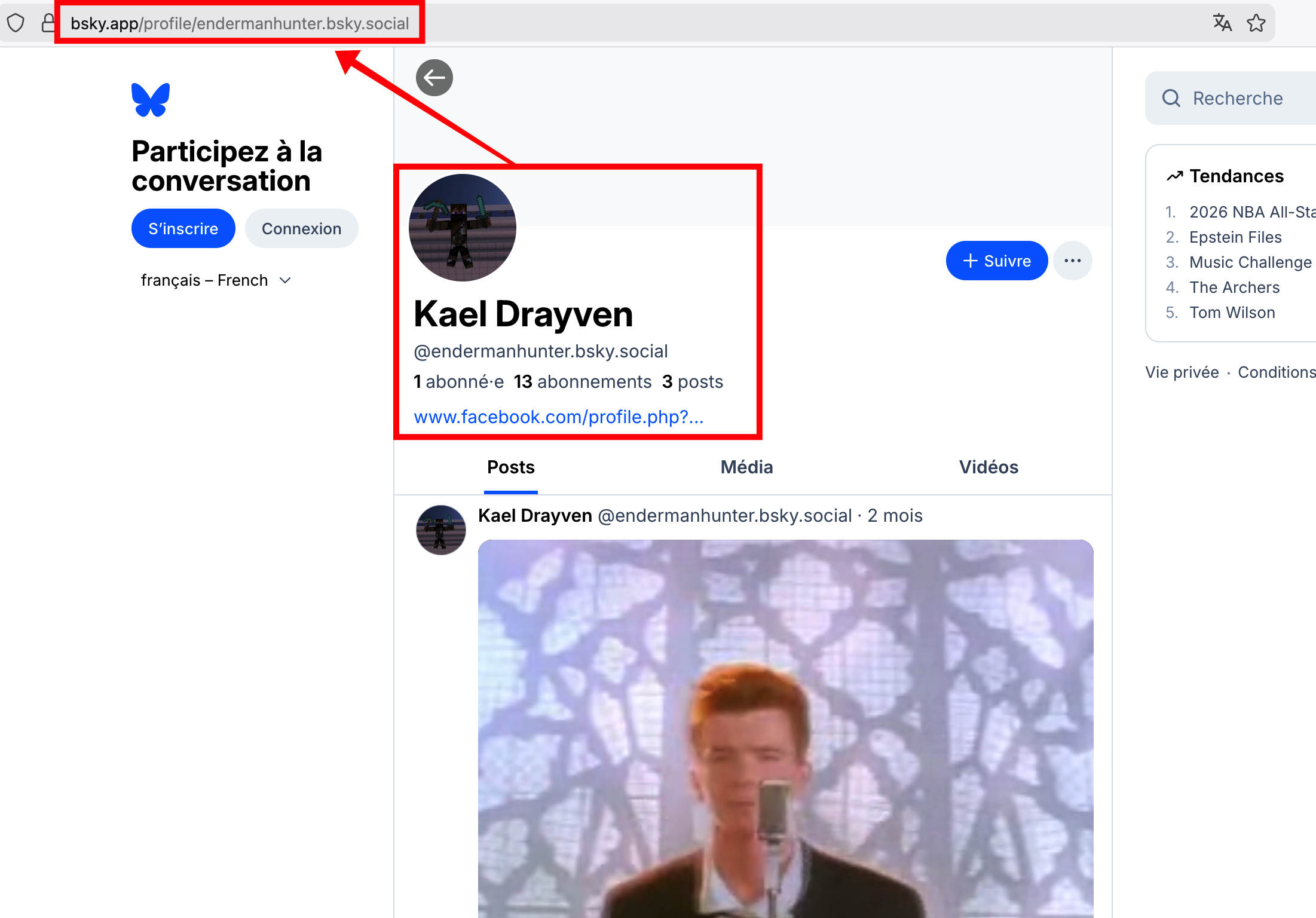
On his Facebook profile, we see that his favorite game is Minecraft and we can obtain his email: kaeldrayven666789@gmail.com.
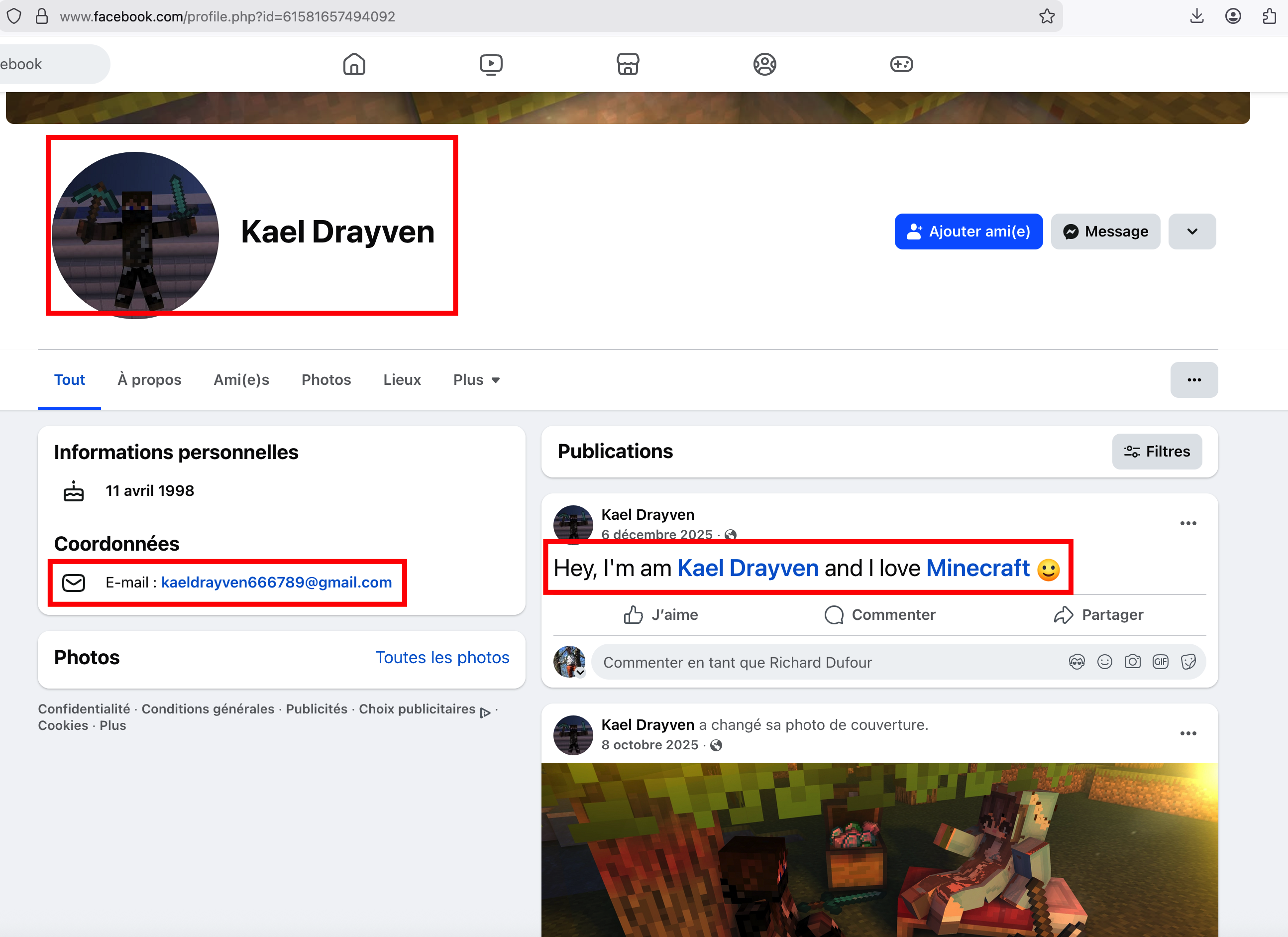
Using a tool such as Epieos (or equivalent) on this email, we find associated Google and Gravatar accounts.
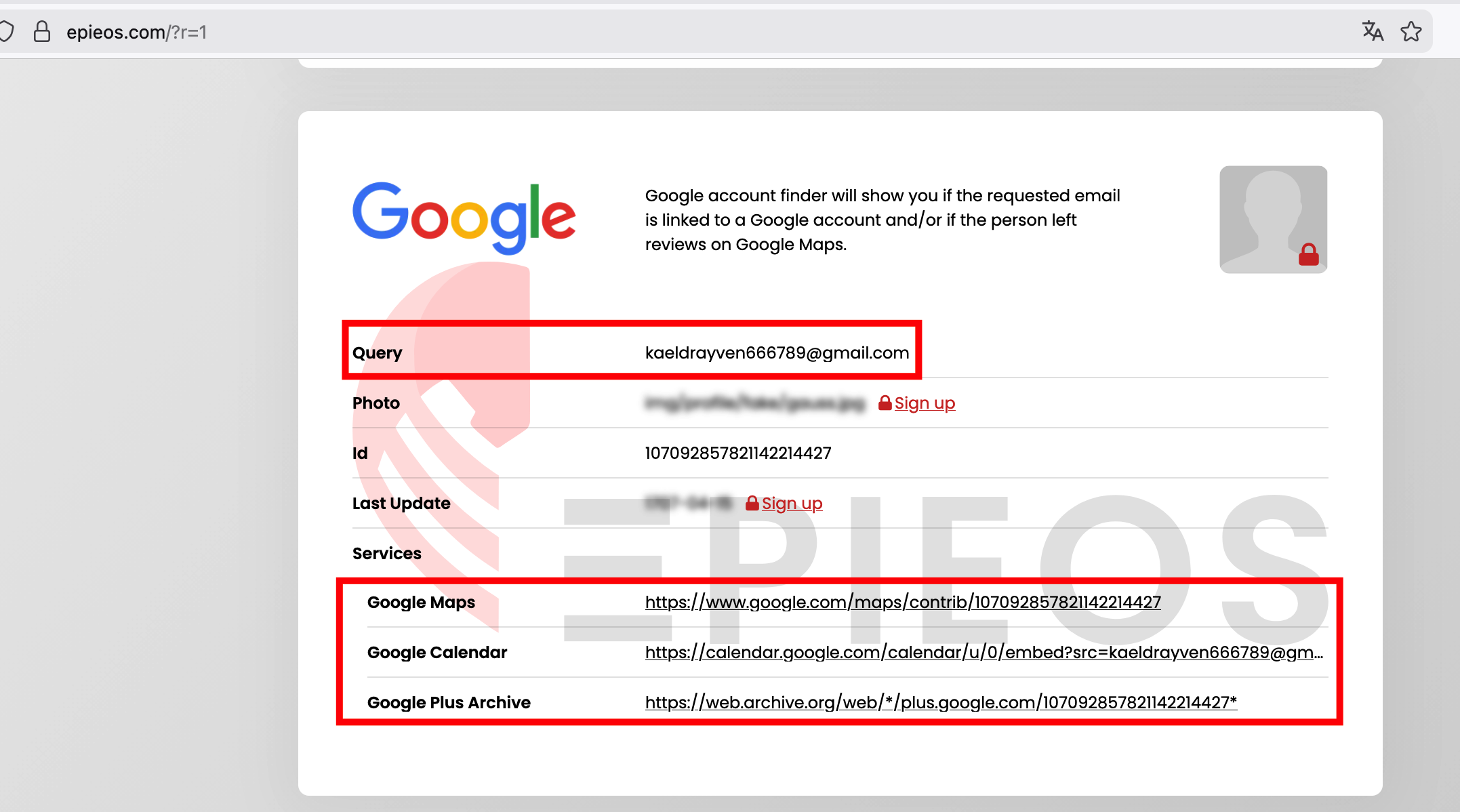
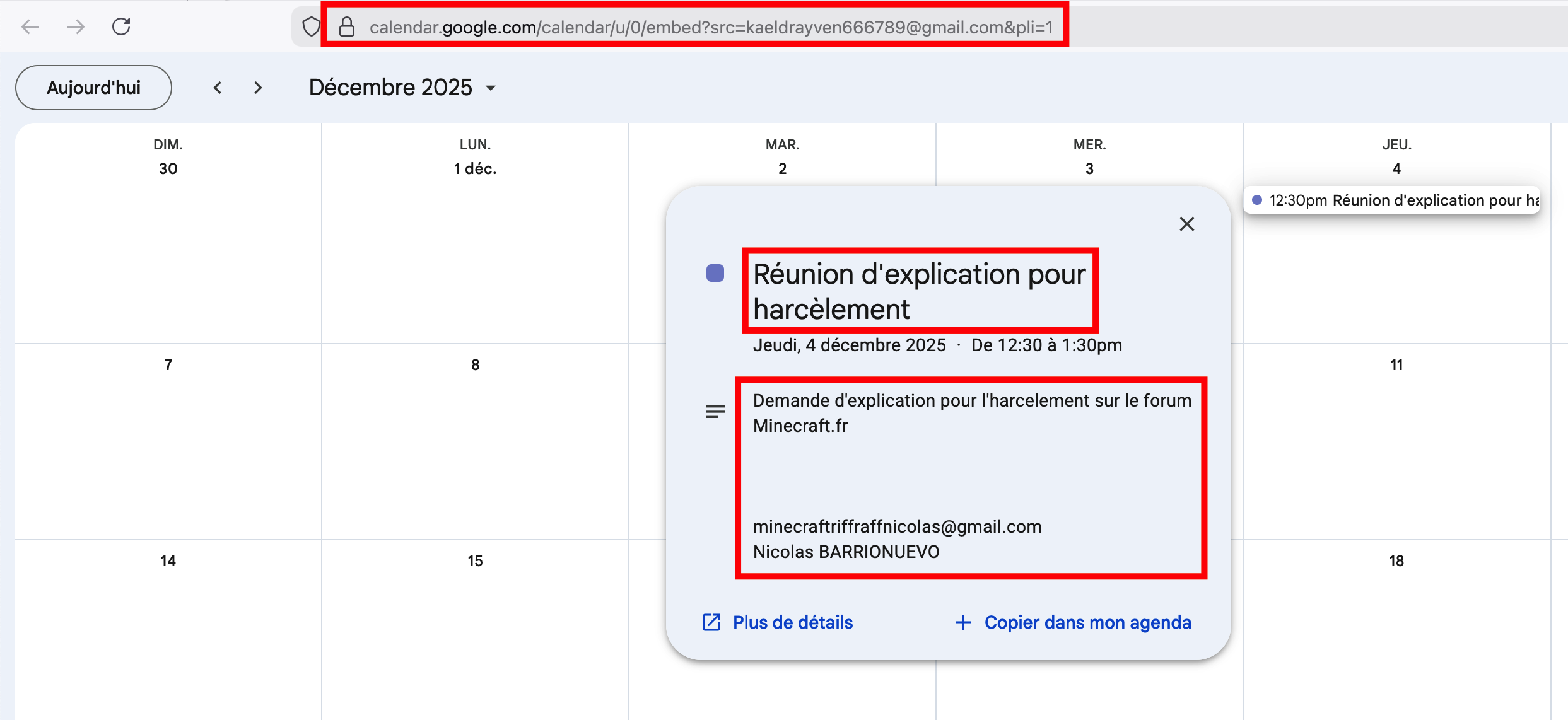
Step 2 — Google Calendar (public event)
Kael’s Google Calendar is public. We find an event on December 4, 2025: “Request for explanation about harassment on the Minecraft.fr forum” (or similar wording).
This event gives us:
- Nicolas BARRIONUEVO
- minecraftriffraffnicolas@gmail.com
- A reference to the minecraft.fr forum
So we have the first first name: Nicolas.
Step 3 — minecraft.fr forum
Searching for “Kael” on the minecraft.fr forum leads to a thread where Nicolas (minecraft-riff-raff) posts a hostile comment about Kael — confirming the first group member.
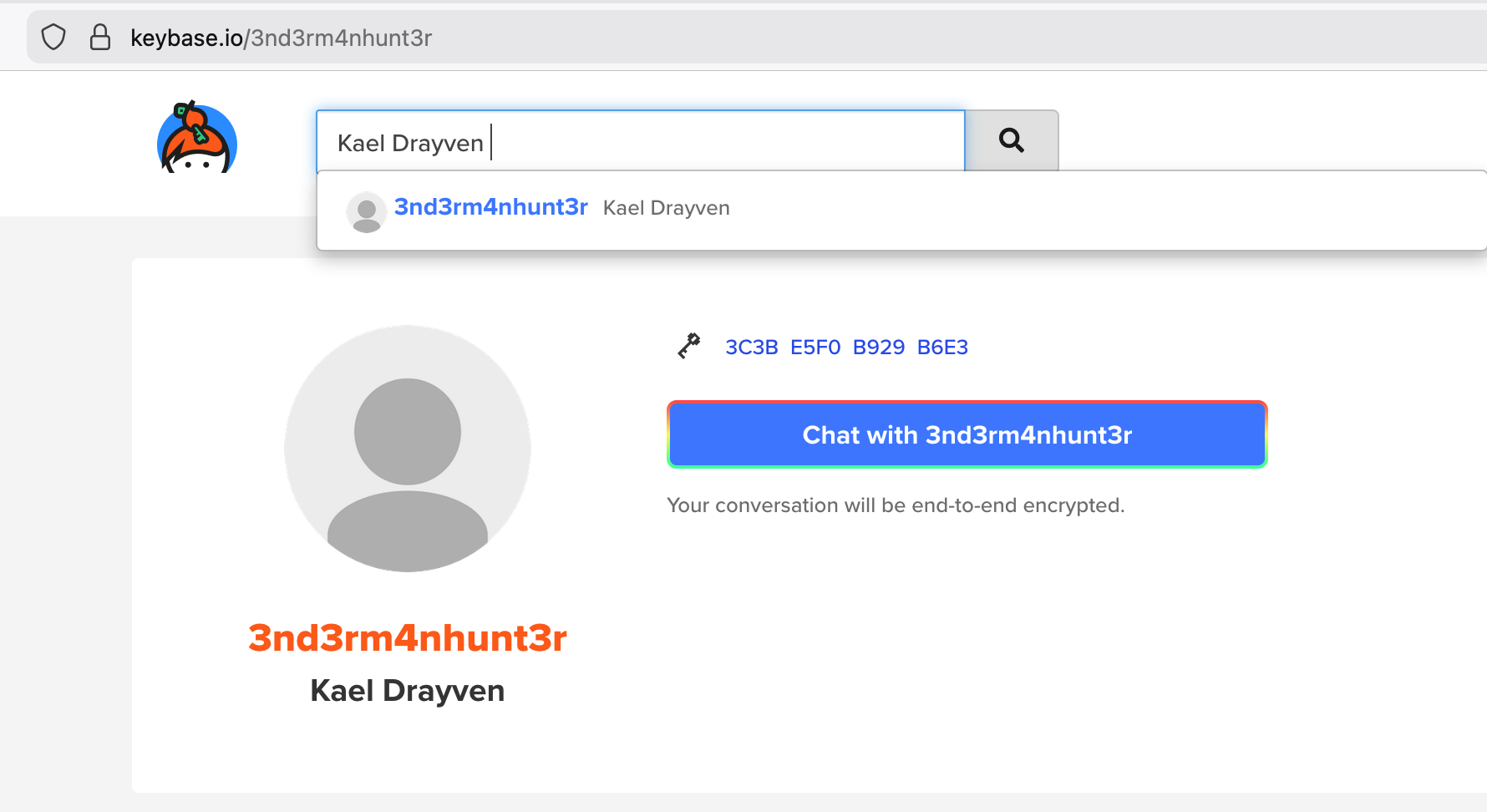
Step 4 — Pivot via Gravatar and Keybase
Using Gravatar (for example https://gravatar.com/site/check with Kael’s email), we find a link to Keybase. On Keybase we find a profile tied to Kael with the nickname 3nd3rm4nhunt3r.
https://gravatar.com/d1d0cbec8c693ed57014133ebae814d572fee4efd8091de4f0e1bb243e4e428e
https://keybase.io/3nd3rm4nhunt3r
Step 5 — WhatsMyName and social networks
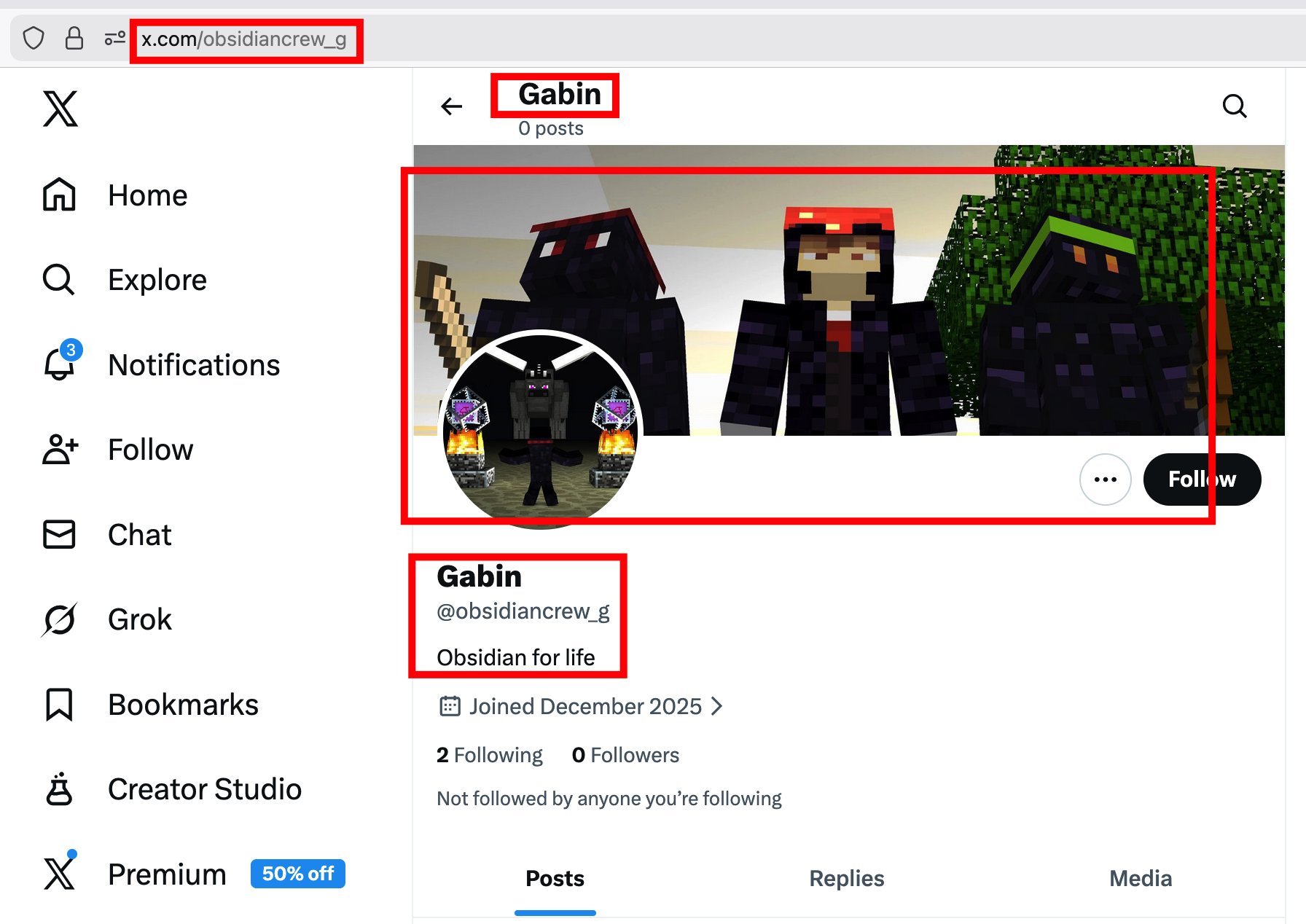
With WhatsMyName (or equivalent) on the nickname 3nd3rm4nhunt3r, we discover accounts on X (Twitter) and TikTok.
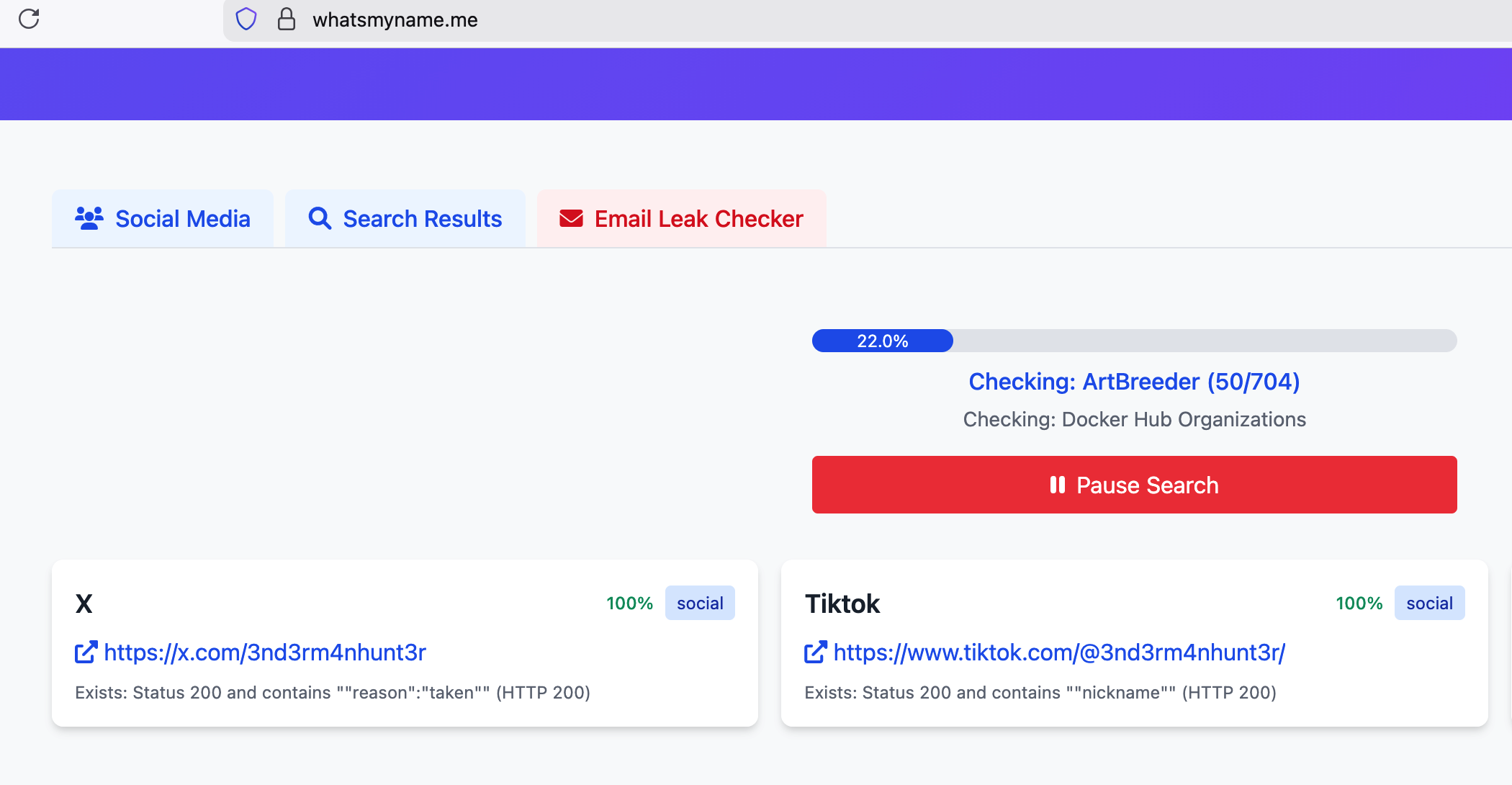
X (Twitter): Kael only has one reply; the person replying is Nicolas.
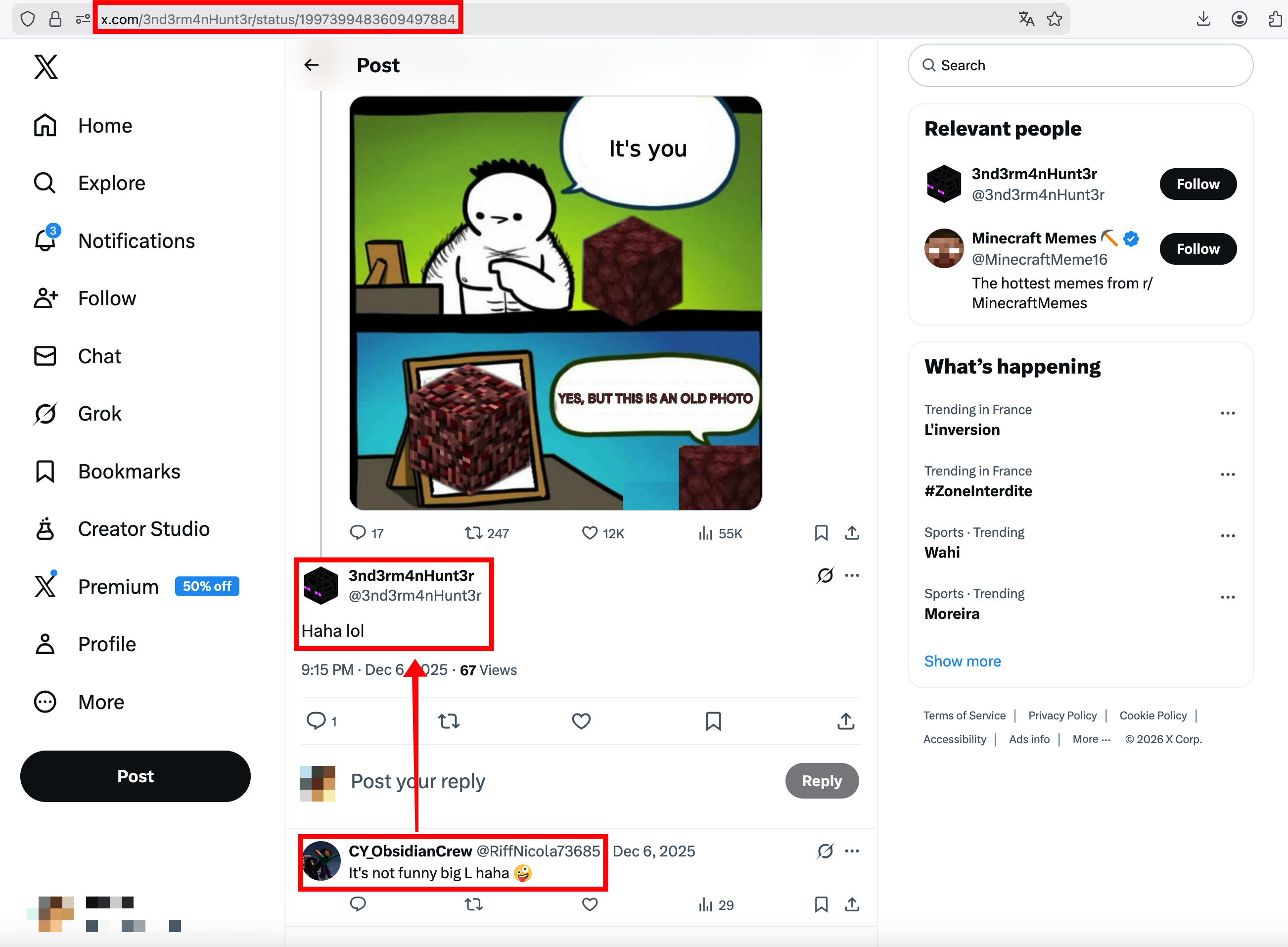
We also see references to ObsidianCrew. By looking at who Nicolas follows (for example @obsidiancrew_g), we find another member whose name is displayed: Gabin — this is the second first name.
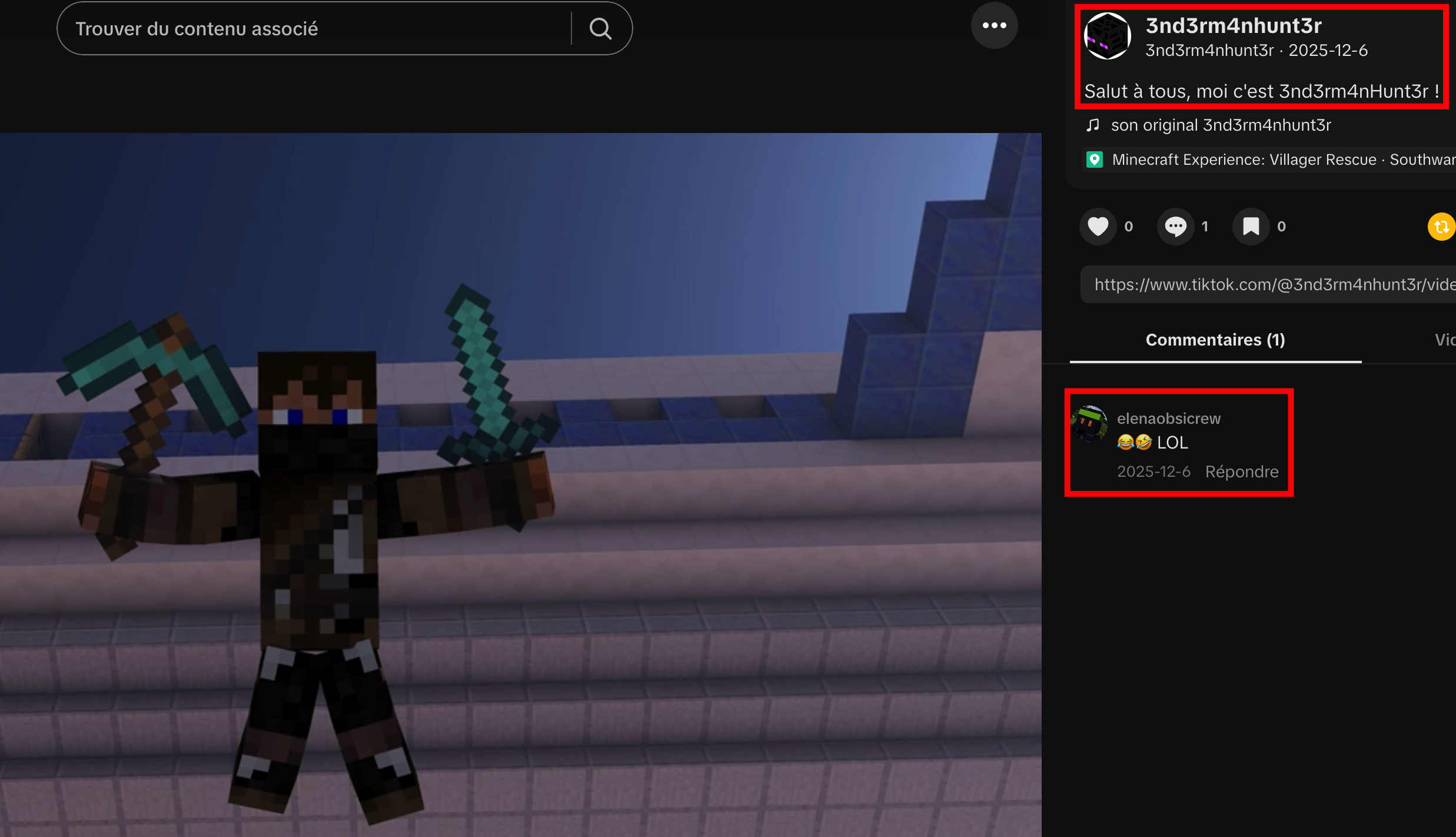
TikTok: Kael has a single post; in the comments we find the third first name: Elena.
Step 6 — Flag
The three first names are Nicolas, Gabin, and Elena, in that order.
Flag: JDHACK{nicolas_gabin_elena}
Smurfed Mario
The challenge sources are available here.
Description
Sometimes, video game characters escape from their worlds… and end up on our walls. This street-art piece is one such example. What was the name of the tea room that used to be located where this artwork now stands?
Flag format:
JDHACK{flag}
Solution
We are given a street-art picture:

Step 1 — Identify the artist and the location
By searching for this type of artwork (for example “pixel art Smurfs street art”) or doing a reverse image search, we discover that it is by IPDO (“I Pixel Di Oplontis”), a duo known for their Smurfs pixel-art pieces. The artist’s page and a marker with the exact location are on Street Art Cities:
- https://streetartcities.com/artists/ipdo
- https://streetartcities.com/markers/fe4cdd94-0d8f-4a4b-8712-664b1cf2c437
The artwork is located at 5 Rue de l’Arbalète, 75005 Paris, France.
Step 2 — Find the former tea room
On Google Maps, at this address, the current Street View may show a restaurant like “Les petits plats de Marc”. Using the historical Street View images (time slider), we go back in time: the place used to be a “Salon de Thé”. Around 2008, the tea room was called Caramelle.
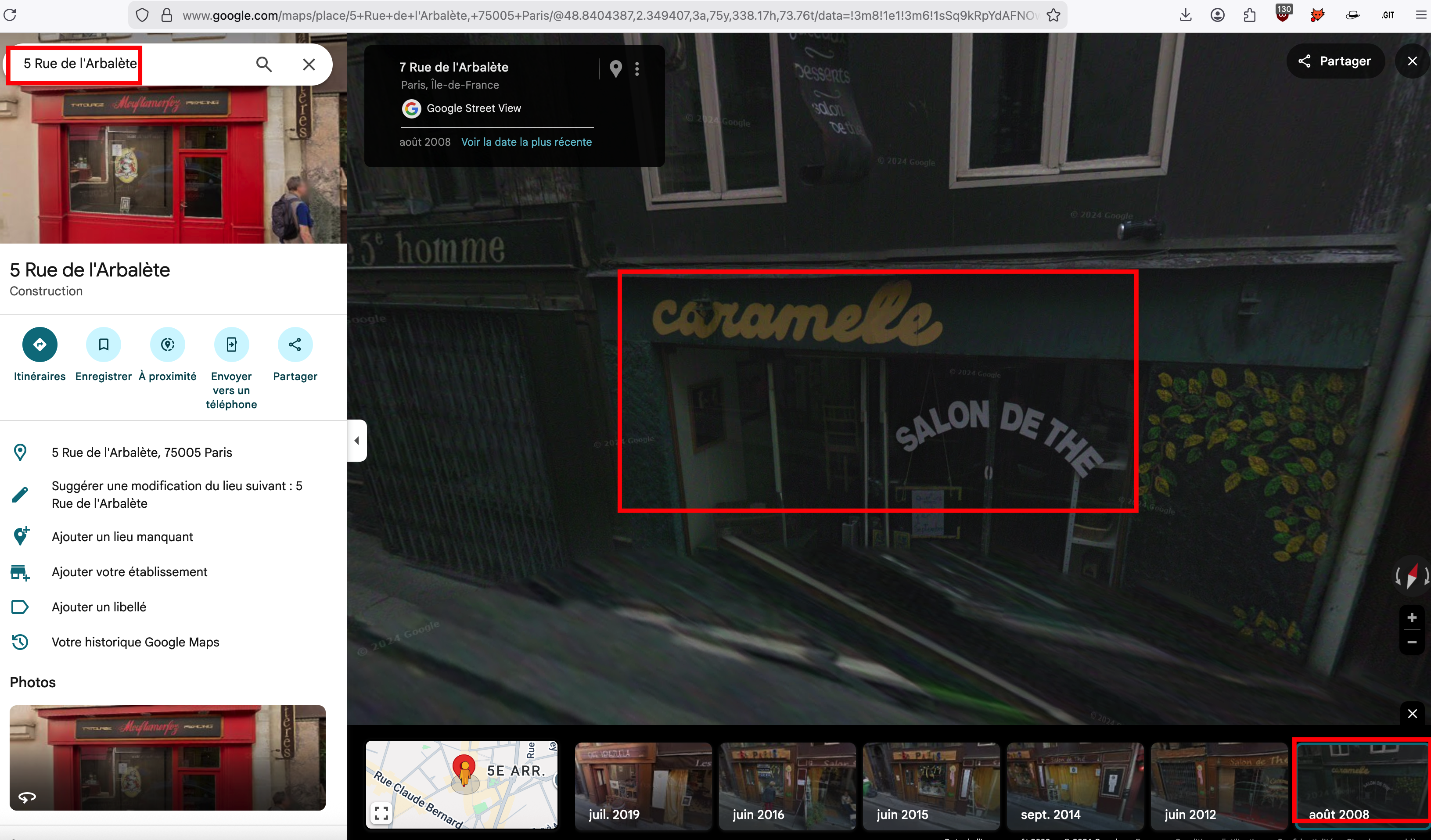
The name of the tea room that used to be at this location is therefore caramelle.
Flag: JDHACK{caramelle}
Difficulty: Extreme
Graal Virtuel (Virtual Grail)
The challenge sources are available here.
Description
In a future where medieval kingdoms and old technologies coexist, the legendary Jeanne d’Arcane sets out in search of the Virtual Grail, an artefact capable of overturning the powers that rule the world. You play as an investigation robot from the Order of the Guardians of Arcane, tasked with finding the Grail before the Imperial Paladins do. One of them, P4l4d1n_1mp3r14l_0f_L1ght, has already left clues behind.
You have access to the Guardians of Arcane Discord, but you do not yet have the Guardian role.
- This extreme challenge has many steps and can take a long time. Good luck! 😉
- Discord is an integral part of this challenge. It is, of course, forbidden to share answers or hints there.
Flag format:
JDHACK{this!is4flag}
Solution
This OSINT challenge has many steps and requires chaining pivots between Discord, usernames, Star Citizen, GitHub, Telegram, Tenor, and finally an archive protected by a password built from an IMO number and aircraft identifiers. We start from the only clue given: P4l4d1n_1mp3r14l_0f_L1ght.
Step 1 — Join the Guardians of Arcane Discord
- Use the invitation link from the challenge: https://discord.gg/Z86d8VBHXR.
- Once you enter, M3rl1n_3xtr4ord1n41r3 welcomes you. Most channels are restricted; only a few (rules, welcome, etc.) are visible.
- The welcome message or the rules explain that to obtain the Guardian role and gain access to the other channels, you must send a password in a private message (DM) to M3rl1n. You will find this password later in the challenge.

The immediate objective is thus: find the secret password that unlocks the Guardian role. Our only concrete clue is the Paladin nickname P4l4d1n_1mp3r14l_0f_L1ght.
Step 2 — Username enumeration: find P4l4d1n_1mp3r14l_0f_L1ght elsewhere
- Use a username search tool to see where this nickname (or close variants) appears. A classic is Sherlock (e.g.
sherlock P4l4d1n_1mp3r14l_0f_L1ght). - Among the results, we find a Star Citizen / Roberts Space Industries (RSI) profile: https://robertsspaceindustries.com/en/citizens/P4l4d1n_1mp3r14l_0f_L1ght.
- Open this profile and read the bio, as well as any links or displayed usernames.
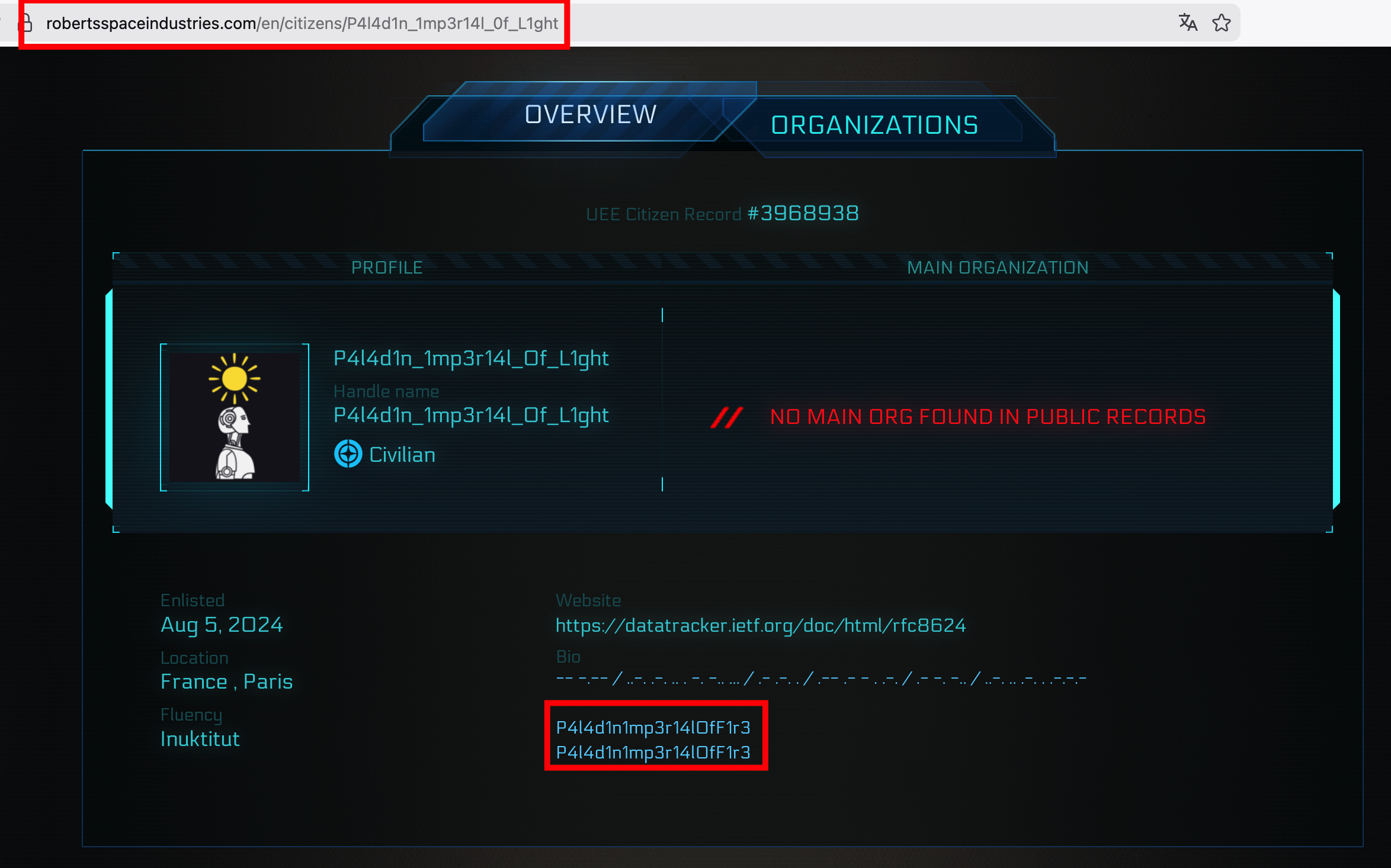
Step 3 — Second Sherlock run: from RSI nickname to GitHub
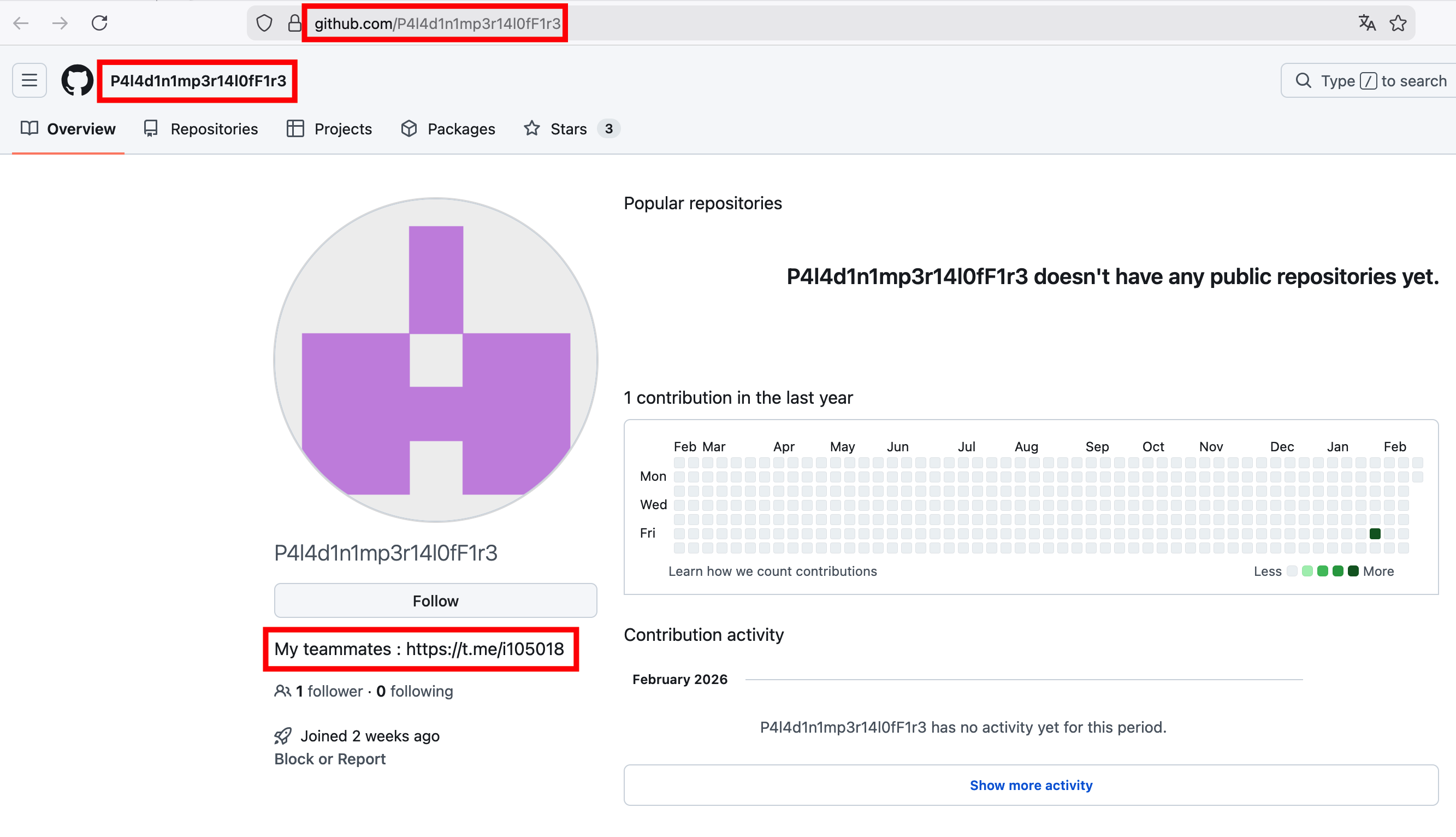
- Run Sherlock again with the nickname from the RSI profile: P4l4d1n1mp3r14l0fF1r3 (with underscores removed, as is often the case on GitHub).
- We find a GitHub account: https://github.com/P4l4d1n1mp3r14l0fF1r3.
- On this GitHub profile, the bio includes: “My teammates: https://t.me/i105018”.
Step 4 — Join the Paladins’ Telegram group
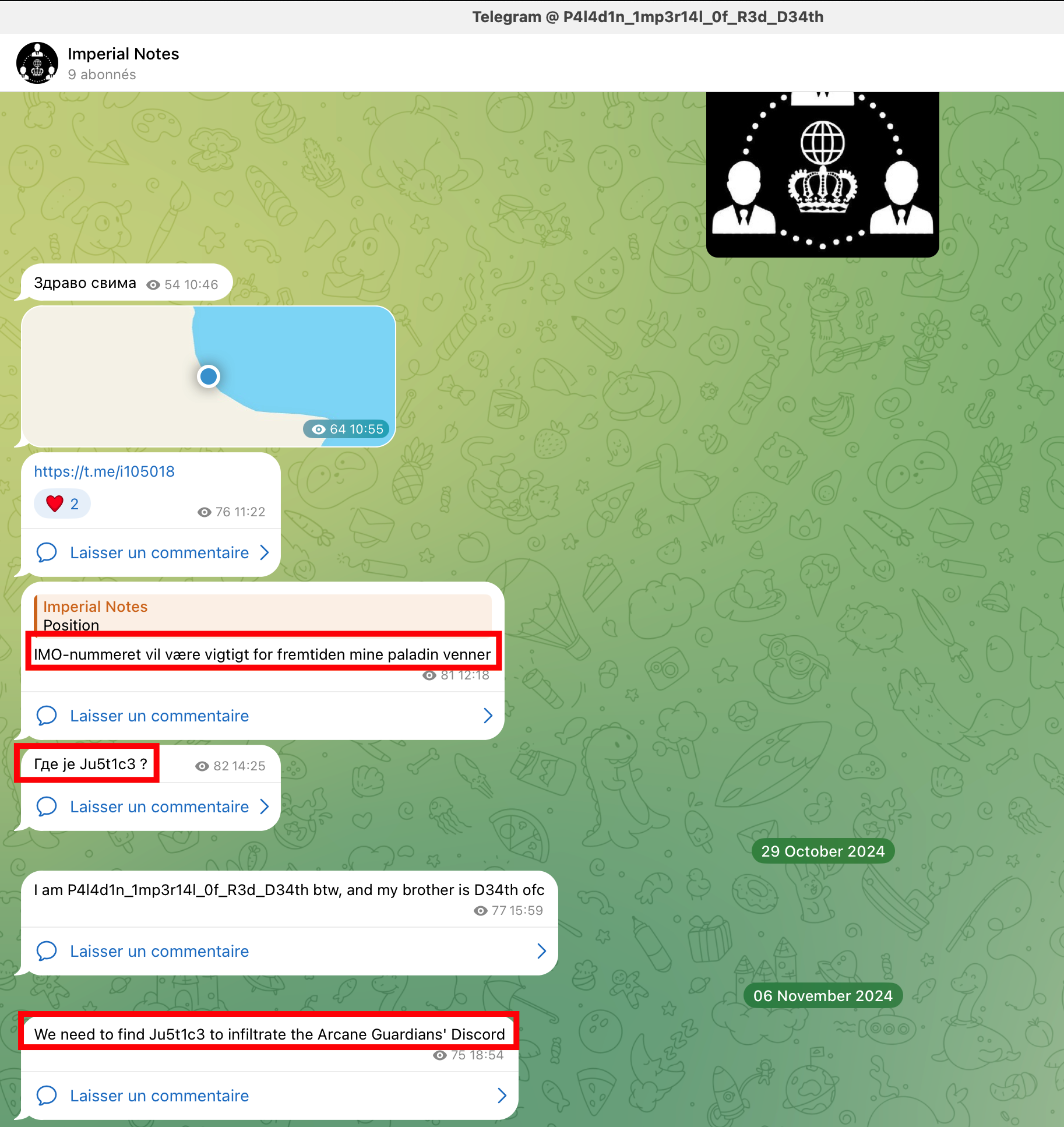
- Join the Telegram group/channel shown in the GitHub bio.
- Read the messages. They are in several languages; one in Danish says that the IMO number will be important later — keep this in mind for the final password.
- Another key message: a Paladin introduces themselves and indicates that Ju5t1c3 is the key to infiltrating the Discord server (to obtain the Guardian password).
- There is also a message about an IMO. Note this IMO clue for later.
Step 5 — Deduce the “Justice” Paladin nickname and find them
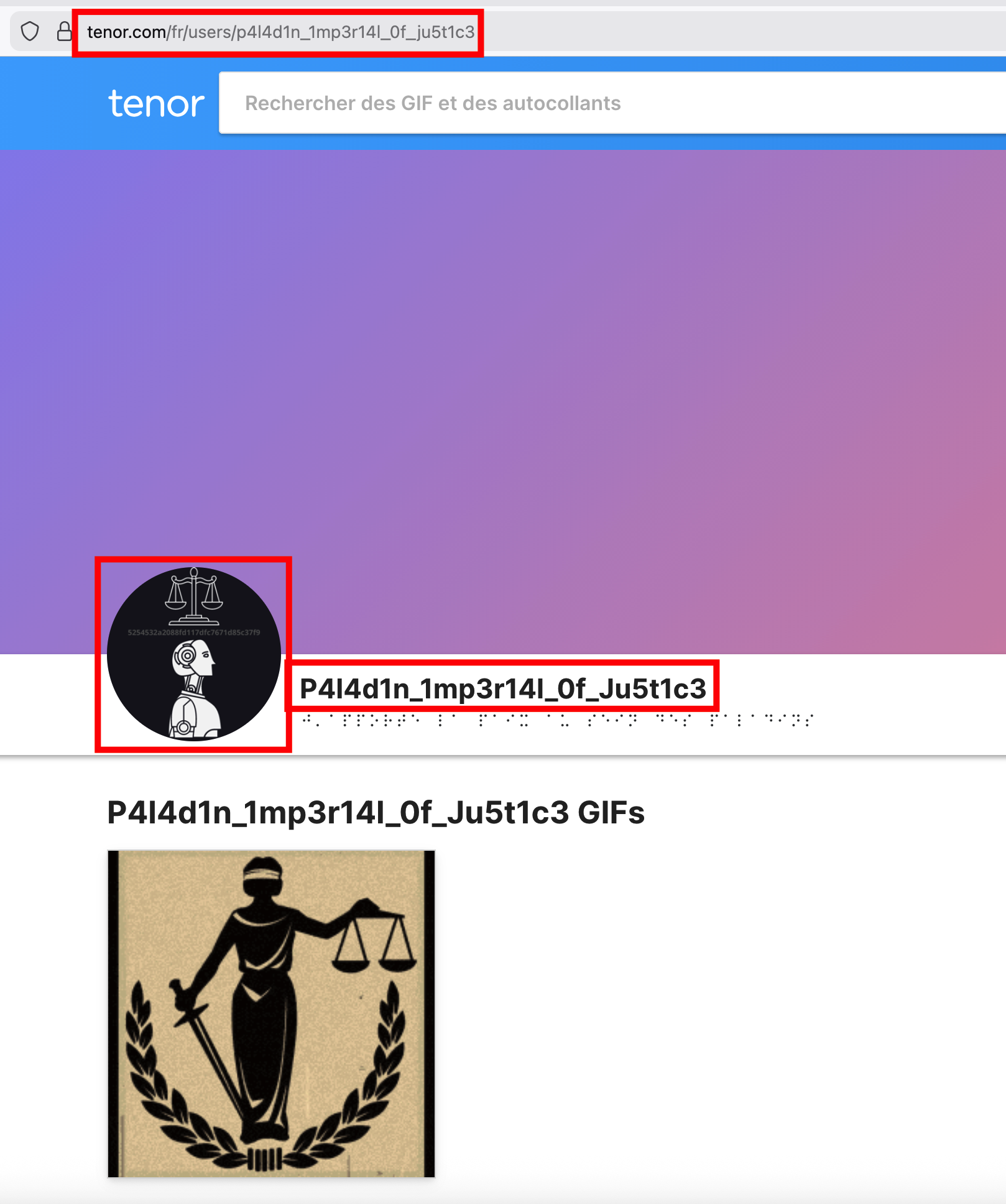
- The Paladins’ nickname pattern is: P4l4d1n_1mp3r14l_0f_XXXXXX (e.g. L1ght, R3d_D34th, D34th). Thus the key “Ju5t1c3” corresponds to P4l4d1n_1mp3r14l_0f_Ju5t1c3.
- Run Sherlock (or manual searches) for P4l4d1n_1mp3r14l_0f_Ju5t1c3 or p4l4d1n_1mp3r14l_0f_ju5t1c3.
- One of the results is Tenor: https://tenor.com/users/p4l4d1n_1mp3r14l_0f_ju5t1c3.
- Open the Tenor profile and look closely at the profile picture. The image contains a hash (MD5-like), for example 5254532a2088fd117dfc7671d85c37f9.
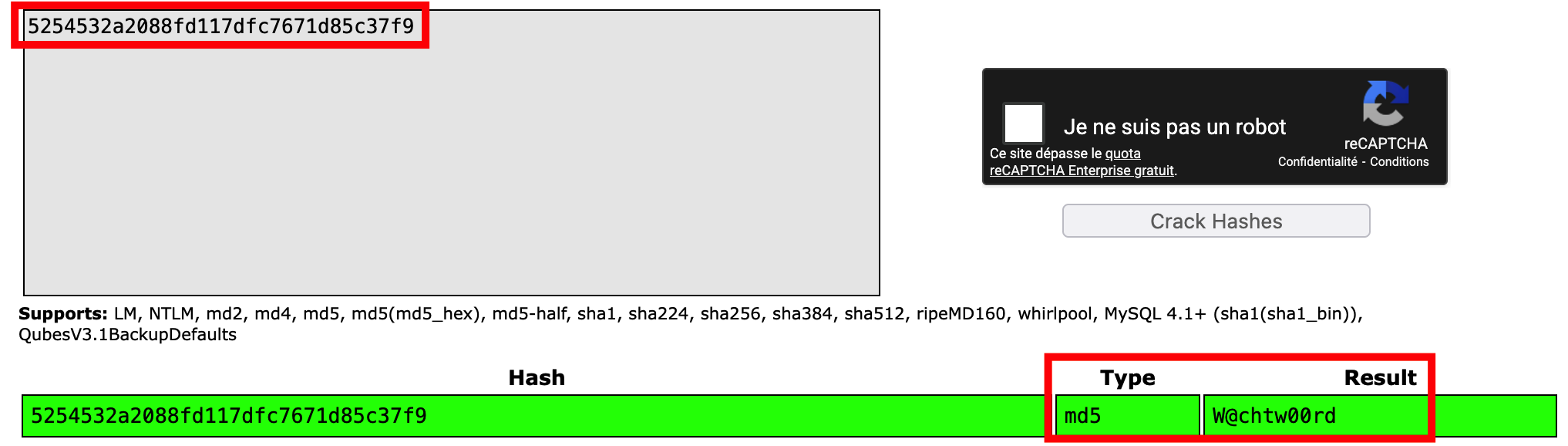
Step 6 — Crack the hash to get the Discord password
- Copy the hash from the Tenor profile picture and use a hash cracking service or tool (e.g. CrackStation, hashes.com, or
hashcat). The hash 5254532a2088fd117dfc7671d85c37f9 is MD5. - CrackStation (or equivalent) reveals the plaintext: W@chtw00rd.
- Go back to Discord and send this password via DM to M3rl1n_3xtr4ord1n41r3. After validation, you receive the Guardian role.
Step 7 — Explore the new Guardian channels
- With the Guardian role, new channels unlock, such as #galerie-des-gardiens and #taverne-des-gardiens.
- #galerie-des-gardiens: contains descriptions of four fictional Guardians — no direct flag.
- #taverne-des-gardiens: M3rl1n posts updates about the Grail quest. One message says that the Paladins obtained a clue and that the Guardians must try to find it and tie it to theirs, and that @0b1-w4n-K3n0b1 has collected and linked the initial clues over time.
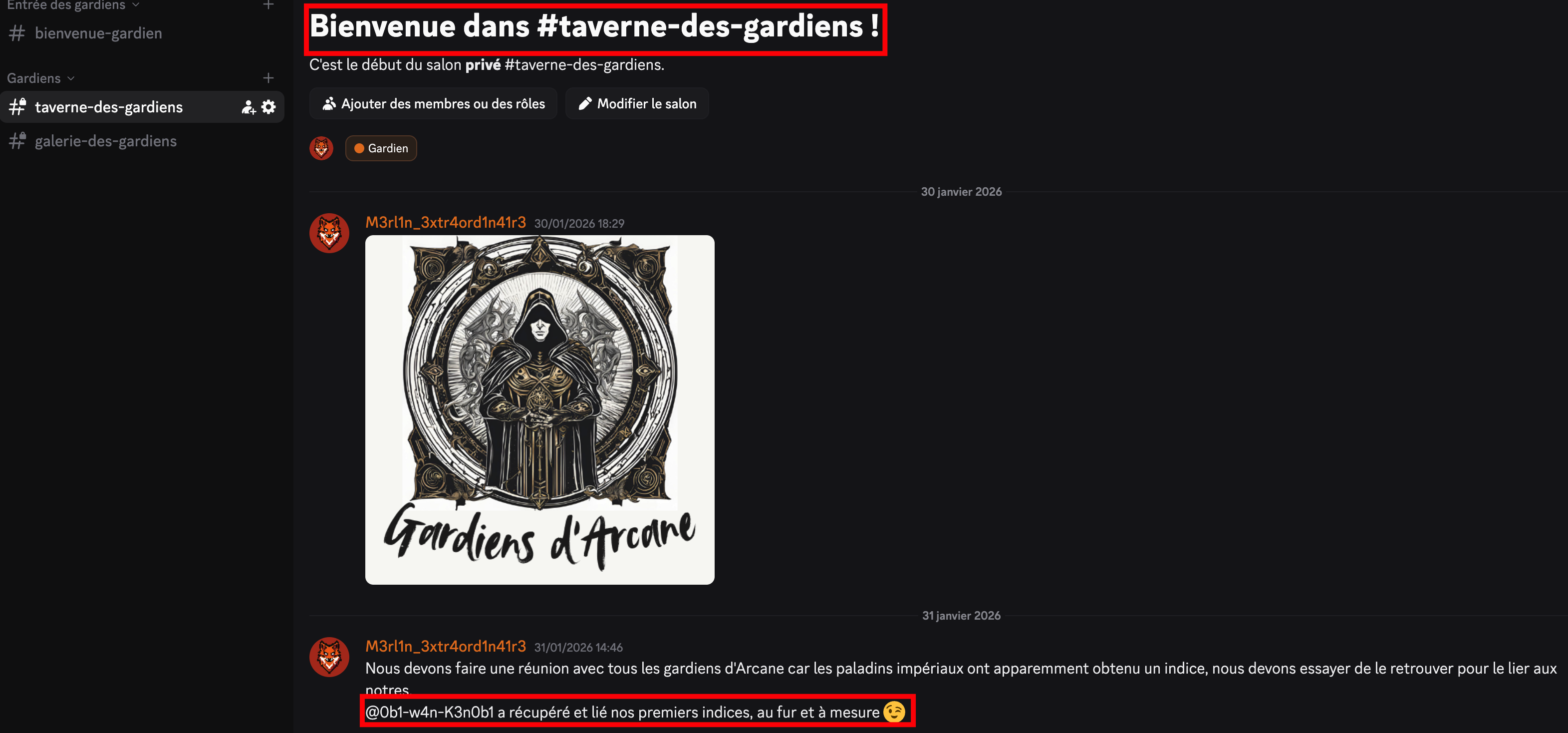
The next pivot is therefore the Discord user 0b1-w4n-K3n0b1.
Step 8 — Find 0b1-w4n-K3n0b1 on GitHub
- Search for 0b1-w4n-K3n0b1 on GitHub (or via Sherlock). We find: https://github.com/0b1-w4n-K3n0b1.
- On this profile, look for a repository related to notes or the Grail — for example a repo named Notes.
- Open this repo and read the README or files. The text explains that 0b1-w4n found the Virtual Grail inside a ZIP file, but the archive is password-protected. To reconstruct the password, you need three pieces of information:
- An OMI/IMO (maritime identification) number,
- The serial number of a DC-3 plane,
- The registration number of a DC-6.
- The password format is:
OMI/IMO + DC3_SERIAL_NUMBER + DC6_REGISTRATION(concatenated, no spaces — e.g.734905317171F-ZBBU).
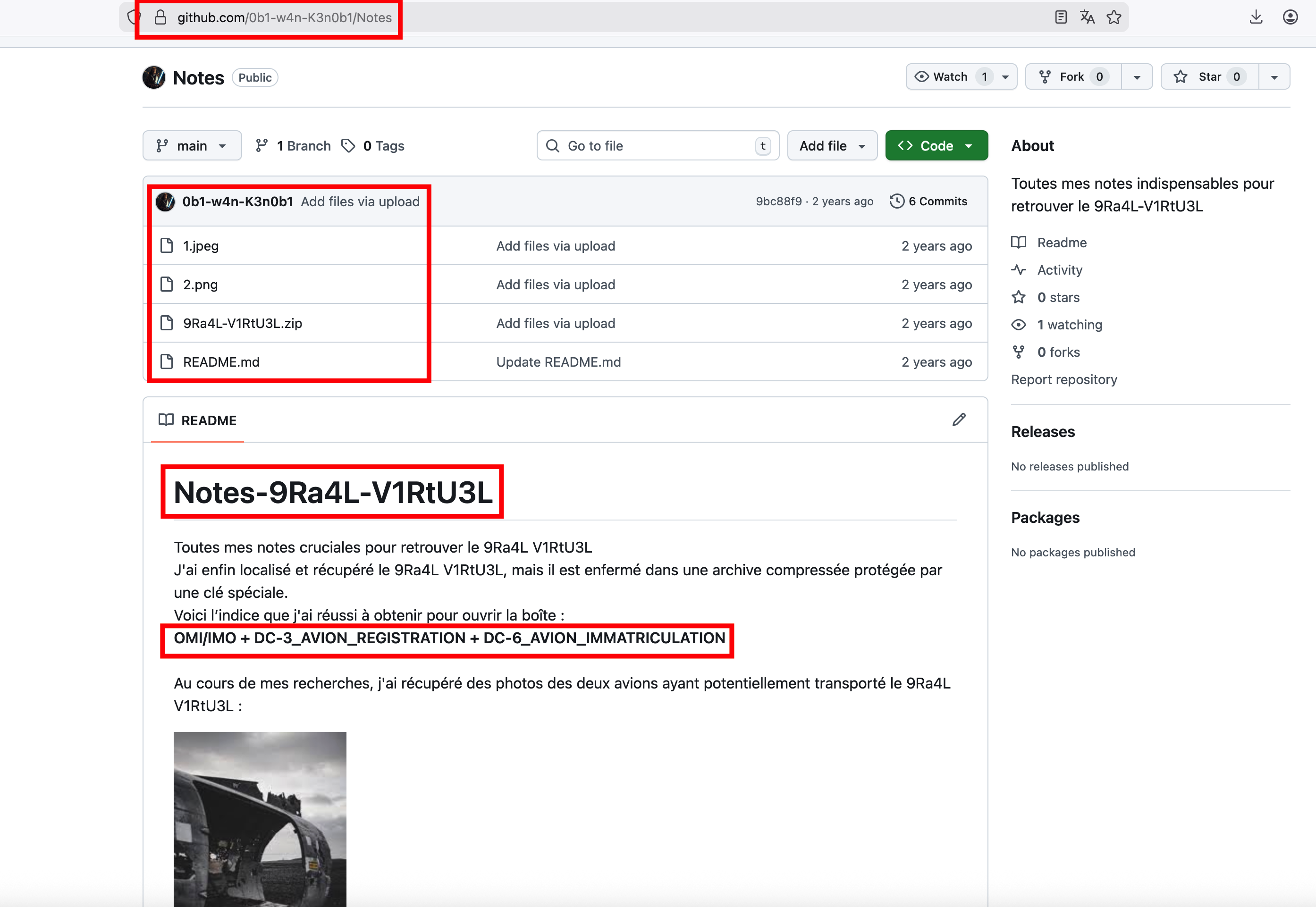
- The repo can also contain two pictures of plane wrecks (one DC-3, one DC-6). These are the hints for the serial number and registration.
Step 9 — Identify the DC-3 wreck (serial number)
- Take the first wreck picture (the DC-3 type). Run a reverse image search (Google Images, Yandex, TinEye, etc.).
- We end up at the wreck of the DC-3 at Sólheimasandur in Iceland (e.g. voyage-islande.fr, Wikipedia — 1973 Sólheimasandur Douglas C-117D crash). The C-117D is a military variant of the DC-3.
- In aviation articles or databases, the serial number of this aircraft is 17171.
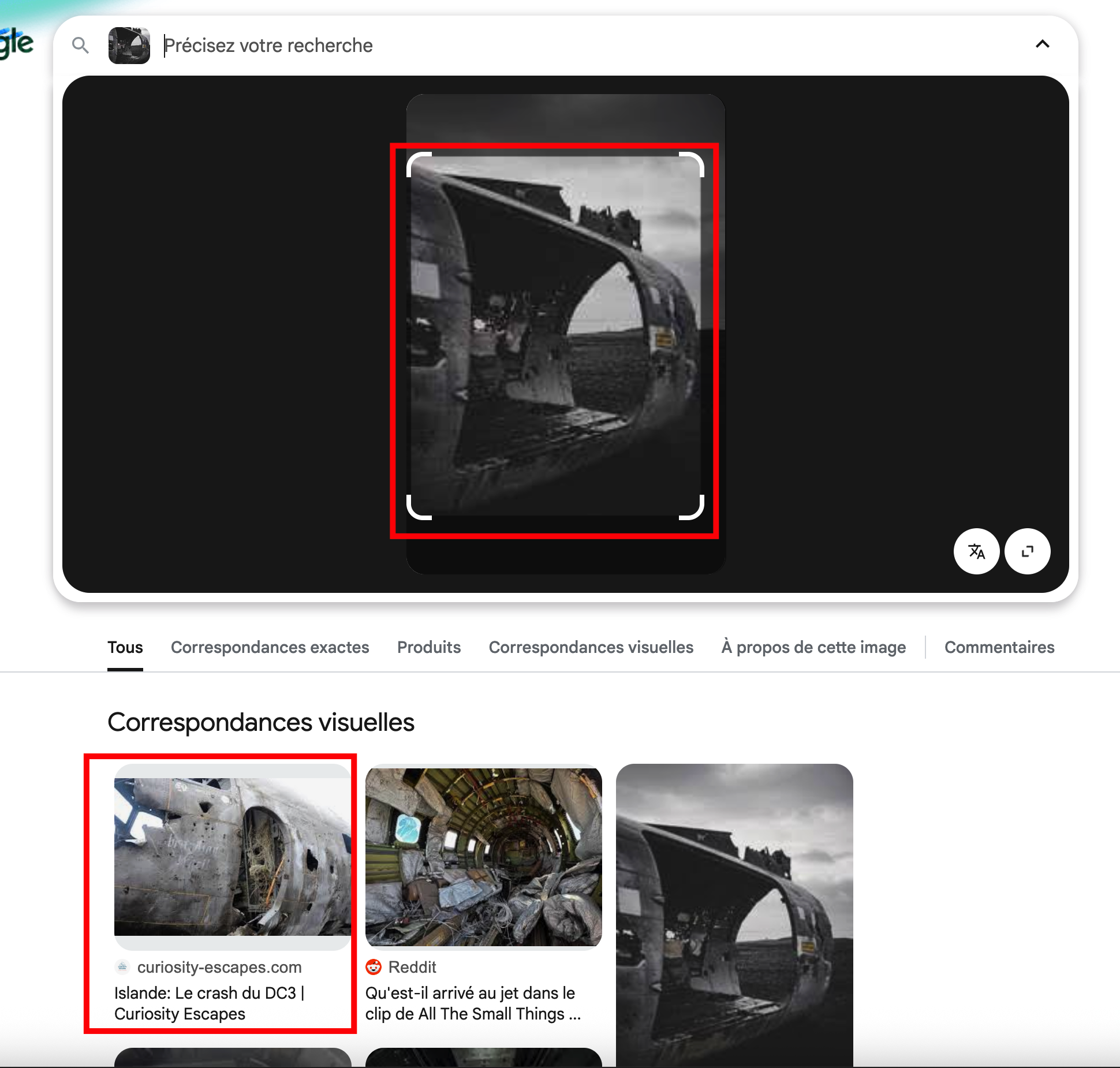
So: DC-3 serial number = 17171.
Step 10 — Identify the DC-6 wreck (registration)
- Take the second wreck picture (the DC-6 type). Run another reverse image search.
- We find the DC-6 of L’Éperthus (France), e.g. aerosteles.net — stelefr-leperthus-dc6.
- This aircraft’s registration is F-ZBBU.
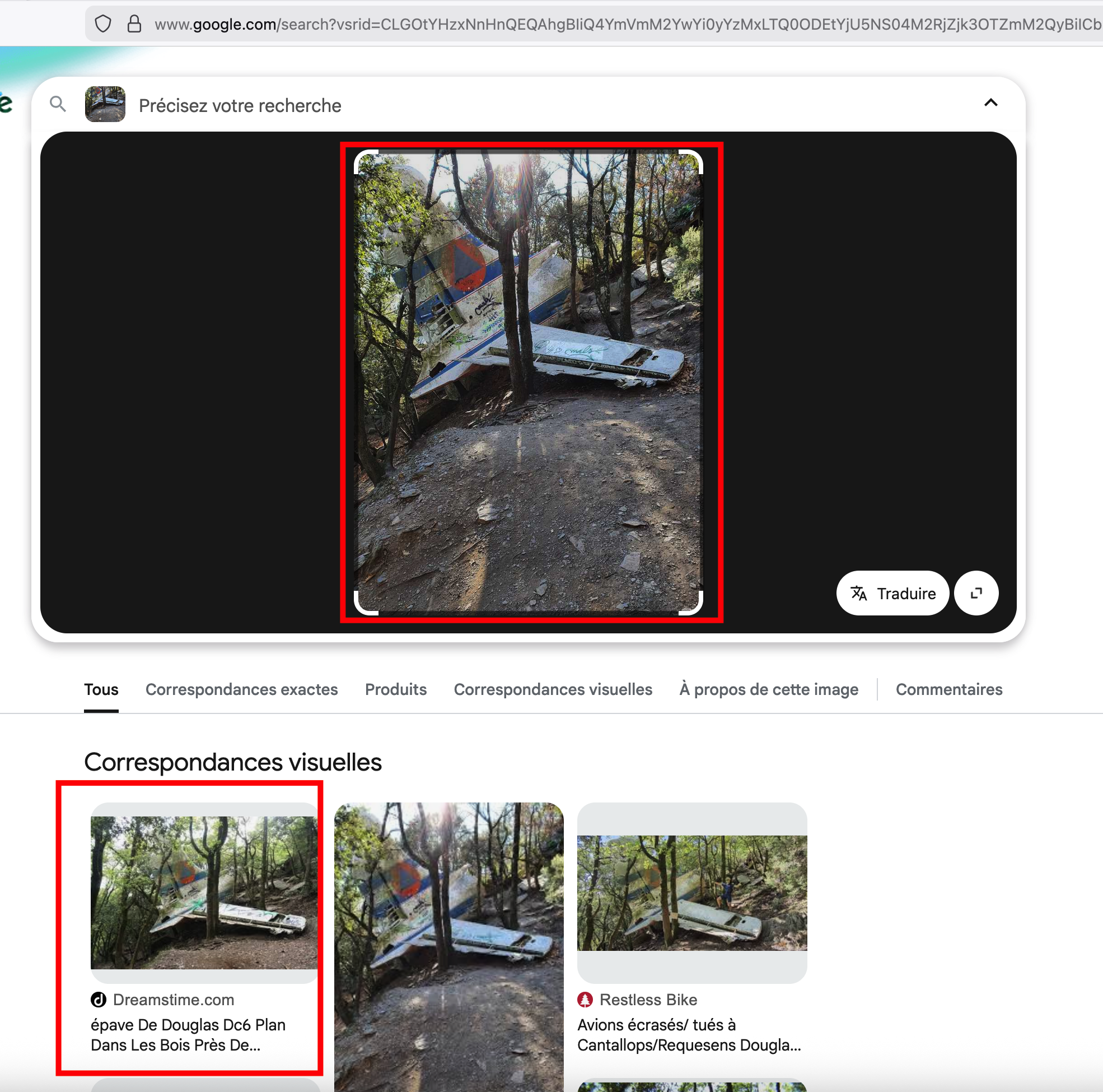
So: DC-6 registration = F-ZBBU.
Step 11 — Find the IMO number using the Telegram coordinates
- Recall the coordinates from the Telegram map: -9.023421, 160.122665 (Pacific Ocean, Solomon Islands).
- Enter them into Google Maps. We see a large shipwreck.
- Identify the vessel: it is the MS World Discoverer (a cruise ship that ran aground in 2000 in the Solomon Islands). Wikipedia or maritime databases list its IMO number as 7349053.
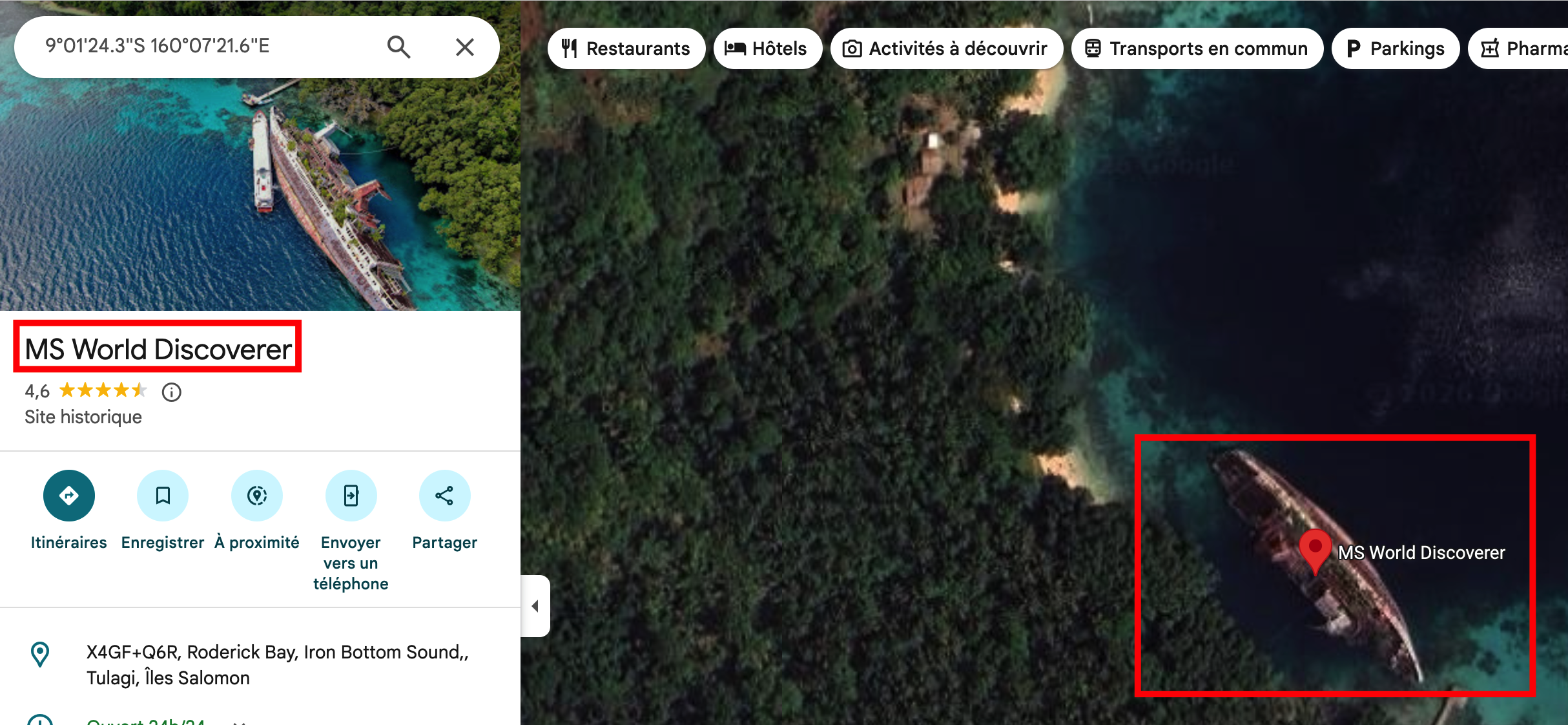
So: IMO = 7349053. The Danish message on Telegram confirms how important this number is.
Step 12 — Build the ZIP password and extract the Grail
- Build the password as indicated: IMO + DC-3 serial number + DC-6 registration → 7349053 + 17171 + F-ZBBU → 734905317171F-ZBBU.
- Download the ZIP file from the 0b1-w4n repo (or from the link mentioned in the Notes).
- Unzip it using the password 734905317171F-ZBBU. Inside, you find a file (text or image) containing the flag.

Flag: JDHACK{CeluiQU!ATTRaP3cEgraalM3Ritelap1USGRandeDesBI3RES}